Cyber Law
Facebook Cyber Laws of IndiaWhat’s covered?
Facebook posts
Messages
Comments etc.
Even “liking” or “sharing” these posts could get a person into trouble....
Top 16 Hackers Friendly Linux OS
16 Hackers Friendly Linux OS
Kali Linux OS:
One of the most advanced penetration-testing platform developed by offensive security. Its flavors are available in both...
Linux Password Stored Format in /etc/passwd
This was Linux users file, to understand linux password file /etc/shadow
2 – Phase Commit Protocol
Commit Protocol
In transaction processing, databases & comp. n/w, the 2 Phase commit is a type of atomic commitment protocol ( ACP ). It...
Making Sense of NoSQl
Book Description:
If you want to understand and perhaps start using the new data storage and analysis technologies that go beyond the SQL database model,...
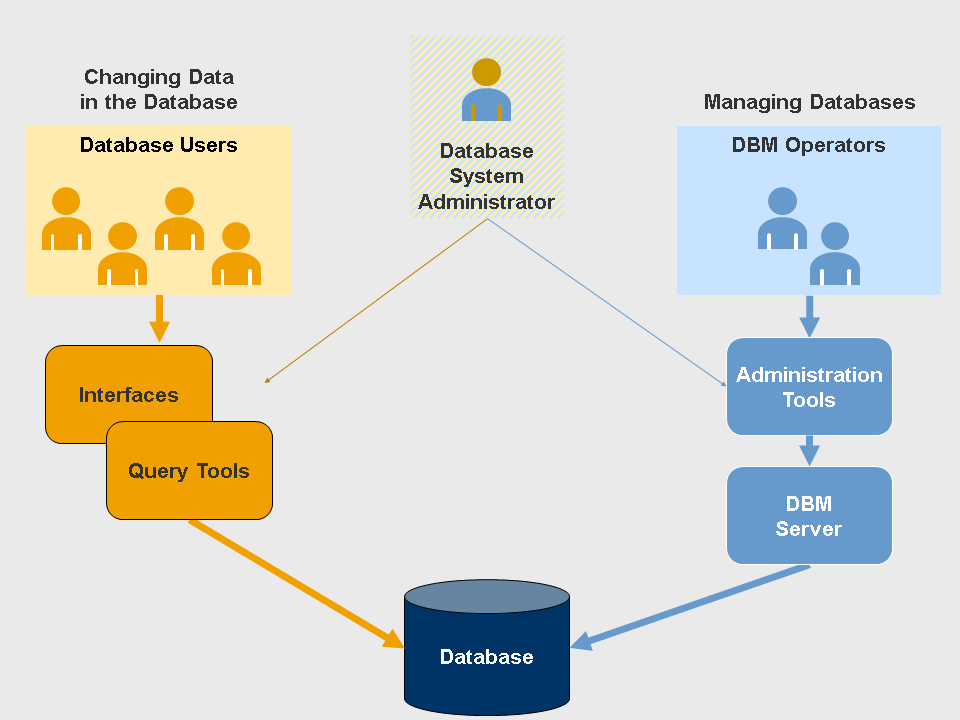
Database Users
Database End Users
End users are the people whose jobs require access to the database for querying, updating and generating reports; database primarily exists for...
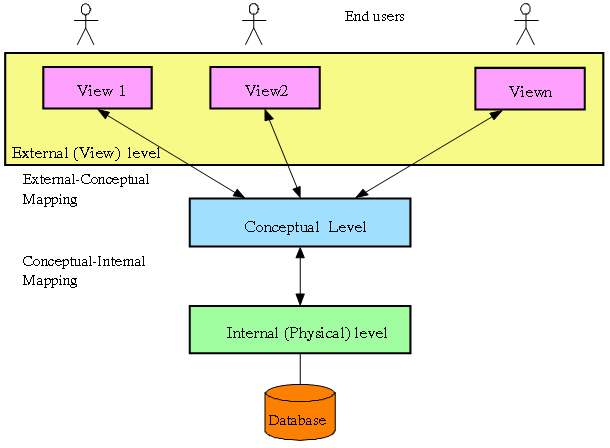
Database 3-Level Architecture
External Level :
The User’s view of the database
Consists of a no. of different external views of the DB
Describes part of the...
Linux Server Hacks
Book Description:
Linux Server Hacks is a collection of 100 industrial-strength hacks, providing tips and tools that solve practical problems for Linux system administrators. Every...
Masking and IP Addressing format
Types of Addressing
Classful Addressing
Classless Addressing
Classful Addressing
IPv4 uses concept of classes. This architecture is called classful addressing
Types of Classes
Class...
Represent Decimal > 8-Bit Notation
Denoting decimal ( Base 2 ) numbers into 8-Bit Binary Notation
eg. 255 in binary = 11111111
16 in binary = 00010000