Is Your Digital Ad Campaign at Risk?
The rise of digital ad fraud has been a nightmare for businesses and marketers alike. Sophisticated bots can easily imitate human behavior and generate...
OpenAI Launched Bug Bounty Program
It’s been almost half a year since the revolutionary ChatGPT was released. Amazingly, it reached 100 million users in just two months.
ChatGPT has...
The Service Accounts Challenge: Can’t See or Secure Them Until It’s Too Late
Here's a hard question to answer: 'How many service accounts do you have in your environment?'. A harder one is: 'Do you know...
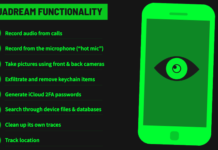
Israel-based Spyware Firm QuaDream Targets High-Risk iPhones with Zero-Click Exploit
Threat actors using hacking tools from an Israeli surveillanceware vendor named QuaDream targeted at least five members of civil society in North America,...
iPhones Hacked Via iOS Zero-Click Exploit To Deploy Spyware
Microsoft Threat Intelligence experts say a threat group is associated with “QuaDream,” an Israeli-based private sector offensive actor (PSOA).
It employed a zero-click exploit called...
Pay $20K To Infect Android Devices via Google Play
In recent times, it has been observed by the security researchers at Kaspersky’s SecureList that the official Google Play store’s security has become increasingly...
Urgent: Microsoft Issues Patches for 97 Flaws, Including Active Ransomware Exploit
Apr 12, 2023Ravie LakshmananPatch Tuesday / Software Updates
It's the second Tuesday of the month, and Microsoft has released another set of security updates...
Fake Google Chrome Error Screens To Inject Malware
Researchers detect a new malware campaign that uses a web page with fake Google Chrome error screens, and the campaign actively distributing malware since...
Lazarus Sub-Group Labyrinth Chollima Uncovered as Mastermind in 3CX Supply Chain Attack
Apr 12, 2023Ravie LakshmananSoftware Security / Cyber Attack
Enterprise communications service provider 3CX confirmed that the supply chain attack targeting its desktop application for...
[eBook] A Step-by-Step Guide to Cyber Risk Assessment
Apr 11, 2023The Hacker NewsCybersecurity / Guide
In today's perilous cyber risk landscape, CISOs and CIOs must defend their organizations against relentless cyber threats,...










![[eBook] A Step-by-Step Guide to Cyber Risk Assessment](https://encrypt.co.in/wp-content/uploads/2023/04/eBook-A-Step-by-Step-Guide-to-Cyber-Risk-Assessment-218x150.png)