BlackCat Ransomware Attackers Spotted Fine-Tuning Their Malware Arsenal
The BlackCat ransomware crew has been spotted fine-tuning their malware arsenal to fly under the radar and expand their reach.
"Among some of the more...
Cyber Attacks Against Middle East Governments Hide Malware in Windows logo
An espionage-focused threat actor has been observed using a steganographic trick to conceal a previously undocumented backdoor in a Windows logo in its attacks...
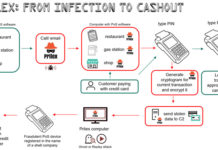
Brazilian Prilex Hackers Resurfaced With Sophisticated Point-of-Sale Malware
A Brazilian threat actor known as Prilex has resurfaced after a year-long operational hiatus with an advanced and complex malware to steal money by...
Hackers Deliver Erbium Password-Stealing Malware
Several popular video games are now being infected with the brand new Erbium malware, which steals personal and sensitive information.
The spread of this malware...
Should You Use a VPN for Online Security? 4 Types of Malware and How...
A VPN creates an encrypted tunnel between your device and the VPN server. All of your data transmissions are protected by the VPN’s encrypted...
Hackers Using PowerPoint Mouseover Trick to Infect System with Malware
The Russian state-sponsored threat actor known as APT28 has been found leveraging a new code execution method that makes use of mouse movement in...
Over 75 Applications on Google Play with 13M Installations Deliver Adware
Researchers from HUMAN’s Satori Threat Intelligence team found a new adware operation named ‘Scylla’, which is the third wave of an attack reported in...
New NullMixer Malware Campaign Stealing Users’ Payment Data and Credentials
Cybercriminals are continuing to prey on users searching for cracked software by directing them to fraudulent websites hosting weaponized installers that deploy malware called...
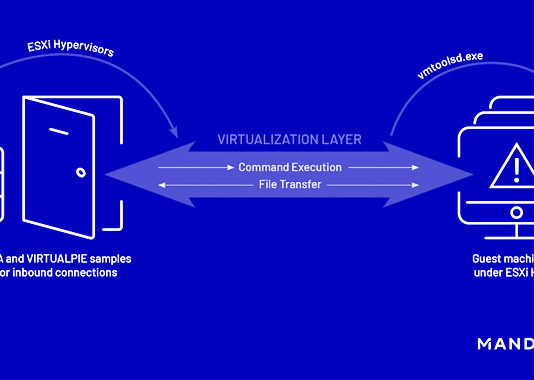
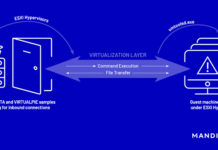
New Malware Families Found Targeting VMware ESXi Hypervisors
Threat actors have been found deploying never-before-seen post-compromise implants in VMware's virtualization software to seize control of infected systems and evade detection.
Google's Mandiant threat...
Cyber Criminals Using Quantum Builder Sold on Dark Web to Deliver Agent Tesla Malware
A recently discovered malware builder called Quantum Builder is being used to deliver the Agent Tesla remote access trojan (RAT).
"This campaign features enhancements and...