CryptoClippy: New Clipper Malware Targeting Portuguese Cryptocurrency Users
Apr 05, 2023Ravie LakshmananCyber Threat / Malware
Portuguese users are being targeted by a new malware codenamed CryptoClippy that's capable of stealing cryptocurrency as...
Fastest Ransomware Ever Found in Ransomware History
Researchers from Checkpoint found a new and previously unknown ransomware variant dubbed “Rorschach” with highly sophisticated features that target U.S. companies.
Rorschach ransomware carries technically...
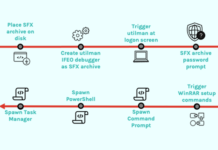
Hackers Using Self-Extracting Archives Exploit for Stealthy Backdoor Attacks
Apr 05, 2023Ravie LakshmananEndpoint Security / Malware
An unknown threat actor used a malicious self-extracting archive (SFX) file in an attempt to establish persistent...
Uber Driver Data Stolen Again From the Servers of Law Firm
Uber faces various cyber attacks that result in the disclosure of employee email addresses, company reports, and information related to IT assets.
The servers of...
Typhon Reborn Stealer Malware Resurfaces with Advanced Evasion Techniques
Apr 05, 2023Ravie LakshmananCyber Threat / Dark Web
The threat actor behind the information-stealing malware known as Typhon Reborn has resurfaced with an updated...
Western Digital Network Breach – Hackers Accessed Servers
Western Digital (WD), a renowned manufacturer of Scandisk drives, has announced a data breach on its network, resulting in unauthorized access to data on...
Microsoft Fixes New Azure AD Vulnerability Impacting Bing Search and Major Apps
Apr 01, 2023Ravie LakshmananAzure / Active Directory
Microsoft has patched a misconfiguration issue impacting the Azure Active Directory (AAD) identity and access management service...
Cacti, Realtek, and IBM Aspera Faspex Vulnerabilities Under Active Exploitation
Apr 01, 2023Ravie LakshmananCyber Attack / Vulnerability
Critical security flaws in Cacti, Realtek, and IBM Aspera Faspex are being exploited by various threat actors...
Deep Dive Into 6 Key Steps to Accelerate Your Incident Response
Mar 31, 2023The Hacker NewsWebinar / Incident response
Organizations rely on Incident response to ensure they are immediately aware of security incidents, allowing for...
Chinese Hackers Using KEYPLUG Backdoor
It has been reported by the Recorded Future’s Insikt Group that RedGolf, a Chinese state-sponsored threat actor group, was using a backdoor designed especially...