Cisco Warns of High-Severity Unpatched Flaw Affecting IP Phones Firmware
Dec 10, 2022Ravie LakshmananEnterprise Security / IP Phones
Cisco has released a new security advisory warning of a high-severity flaw affecting IP Phone 7800...
Chinese Espionage Hackers Target Tibetans Using New LOWZERO Backdoor
A China-aligned advanced persistent threat actor known as TA413 weaponized recently disclosed flaws in Sophos Firewall and Microsoft Office to deploy a never-before-seen backdoor...
Researchers Identify 3 Hacktivist Groups Supporting Russian Interests
At least three alleged hacktivist groups working in support of Russian interests are likely doing so in collaboration with state-sponsored cyber threat actors, according...
Researchers Uncover Covert Attack Campaign Targeting Military Contractors
A new covert attack campaign singled out multiple military and weapons contractor companies with spear-phishing emails to trigger a multi-stage infection process designed to...
Zerobot Botnet Emerges as a Growing Threat with New Exploits and Capabilities
Dec 22, 2022Ravie LakshmananInternet of Things / Patch Management
The Zerobot DDoS botnet has received substantial updates that expand on its ability to target...
LastPass Admits to Severe Data Breach, Encrypted Password Vaults Stolen
Dec 23, 2022Ravie LakshmananPassword Management / Data Breach
The August 2022 security breach of LastPass may have been more severe than previously disclosed by...
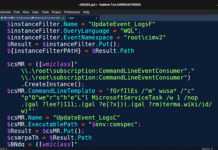
BlackCat Ransomware Attackers Spotted Fine-Tuning Their Malware Arsenal
The BlackCat ransomware crew has been spotted fine-tuning their malware arsenal to fly under the radar and expand their reach.
"Among some of the more...
Experts Uncover 85 Apps with 13 Million Downloads Involved in Ad Fraud Scheme
As many as 75 apps on Google Play and 10 on Apple App Store have been discovered engaging in ad fraud as part of...
Hackers Aid Protests Against Iranian Government with Proxies, Leaks and Hacks
Several hacktivist groups are using Telegram and other tools to aid anti-government protests in Iran to bypass regime censorship restrictions amid ongoing unrest in...
Cyber Attacks Against Middle East Governments Hide Malware in Windows logo
An espionage-focused threat actor has been observed using a steganographic trick to conceal a previously undocumented backdoor in a Windows logo in its attacks...