Malicious actors can take advantage of “insufficient” forensic visibility into Google Cloud Platform (GCP) to exfiltrate sensitive data, a new research has found.
“Unfortunately, GCP does not provide the level of visibility in its storage logs that is needed to allow any effective forensic investigation, making organizations blind to potential data exfiltration attacks,” cloud incident response firm Mitiga said in a report.
The attack banks on the prerequisite that the adversary is able to gain control of an identity and access management (IAM) entity in the targeted organization by methods like social engineering to access the GCP environment.
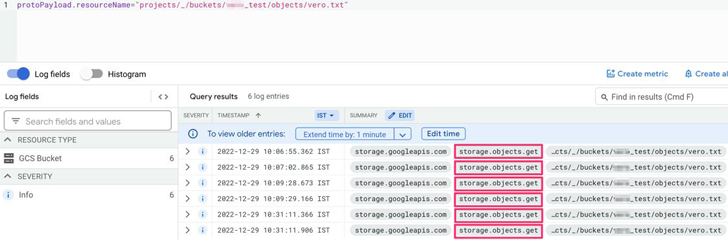
The crux of the problem is that GCP’s storage access logs do not provide adequate transparency with regards to potential file access and read events, instead grouping them all as a single “Object Get” activity.
“The same event is used for a wide variety of types of access, including: Reading a file, downloading a file, copying a file to an external server, [and] reading the metadata of the file,” Mitiga researcher Veronica Marinov said.
This lack of distinction could enable an attacker to harvest sensitive data without being detected, mainly because there is no way to differentiate between malicious and legitimate user activity.
In a hypothetical attack, a threat actor can use Google’s command line interface (gsutil) to transfer valuable data from the victim organization’s storage buckets to an external storage bucket within the attacker organization.
Google has since provided mitigation recommendations, which range from Virtual Private Cloud (VPC) Service Controls to using organization restriction headers to limit cloud resource requests.
The disclosure comes as Sysdig unearthed a sophisticated attack campaign dubbed SCARLETEEL that’s targeting containerized environments to perpetrate theft of proprietary data and software.
Source: thehackernews.com










