The lack of rate-limiting in Instagram was discovered by Gtm Mänôz, a security researcher from Kathmandu, Nepal.
This flaw could have allowed an attacker to bypass Facebook’s two-factor authentication by validating the targeted user’s already-validated Facebook mobile number using the Meta Accounts Center.
Two-Factor Authentication Bypass on Facebook
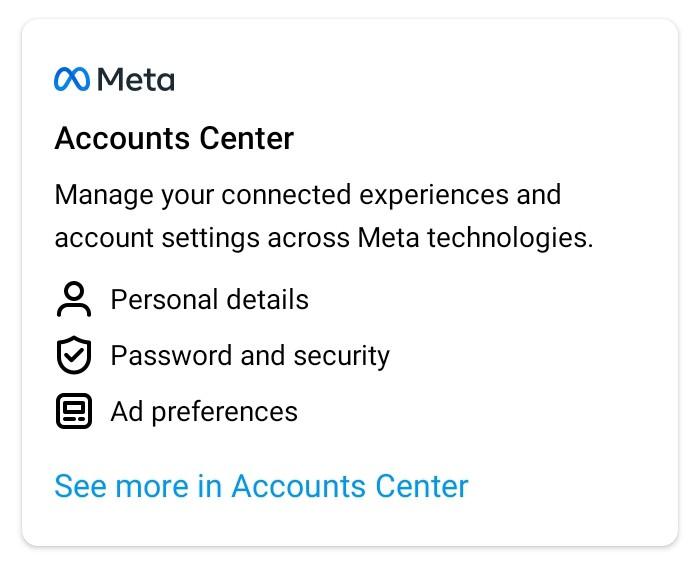
The researcher looked at Instagram’s latest “Meta Accounts Center” layout and noticed that the “Personal Details” section allowed users to add their email and phone number to both their Instagram and linked Facebook accounts. This information can then be verified by entering the proper 6-digit code received by email or phone.
“At the time of reporting, the endpoint verifying the 6-digit code was vulnerable to lack of rate-limit protection allowing anyone to confirm unknown/known email and phone number both in Instagram and linked Facebook accounts”, the researcher explains.

The lack of a rate-limiting feature allowed an attacker to add an already-verified phone number to a target Facebook/Instagram account when Mänôz looked at Instagram’s new layout for “Meta Accounts.”
Facebook generates a one-time code after the user enters their mobile number to confirm their identification.
However, a threat actor may be able to generate unlimited bot traffic to launch a brute-force attack to validate a one-time Facebook PIN to link the accounts, thus bypassing Facebook’s 2FA protections, because of a rate-limiting flaw on Instagram’s endpoint.
According to the researcher, if the phone number was fully verified and 2FA was activated on Facebook, the victim’s account would no longer have 2FA enabled.
Additionally, if the phone number was only partially confirmed, i.e., used for 2FA, the 2FA will be revoked, and the phone number will be deleted from the victim’s account.
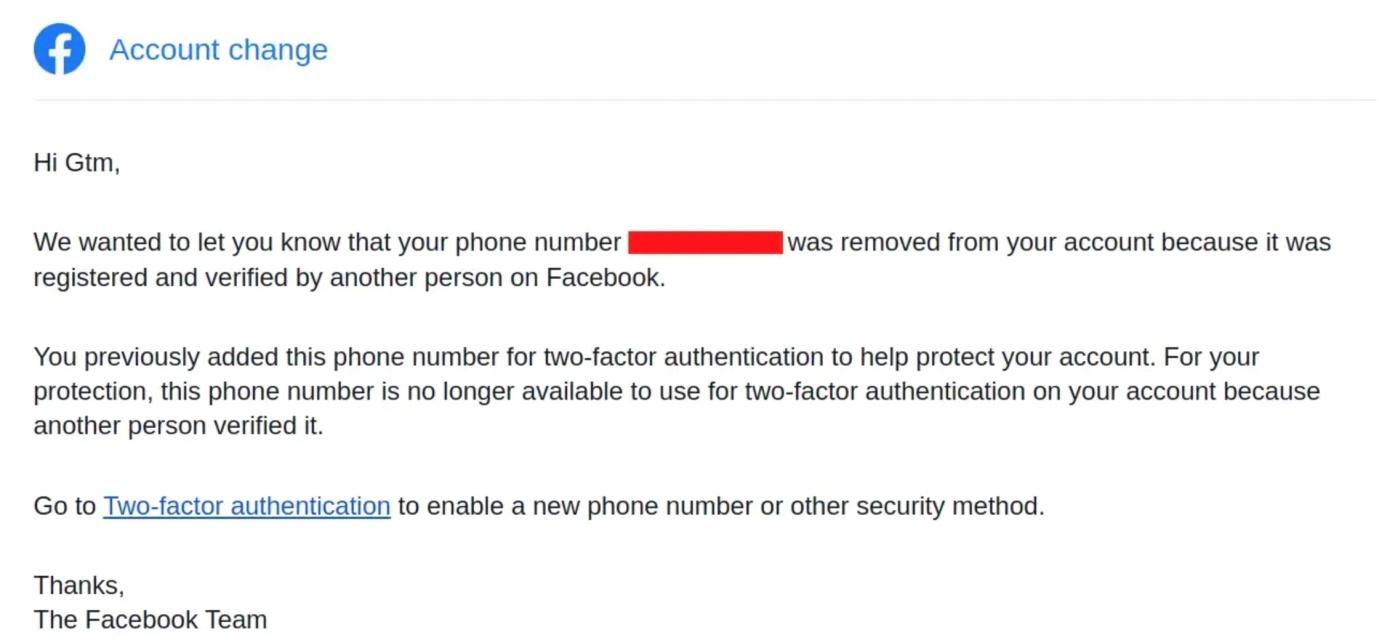
“Basically the highest impact here was revoking anyone’s SMS-based 2FA just knowing the phone number,” according to Mänôz.
Since then, Meta has resolved the issue and as part of its bug bounty programme, it gave Mänôz $27,000. To avoid being exposed, users should upgrade their apps to the most recent version.
Network Security Checklist – Download Free E-Book
Source: gbhackers.com










