An open source command-and-control (C2) framework known as Havoc is being adopted by threat actors as an alternative to other well-known legitimate toolkits like Cobalt Strike, Sliver, and Brute Ratel.
Cybersecurity firm Zscaler said it observed a new campaign in the beginning of January 2023 targeting an unnamed government organization that utilized Havoc.
“While C2 frameworks are prolific, the open-source Havoc framework is an advanced post-exploitation command-and-control framework capable of bypassing the most current and updated version of Windows 11 defender due to the implementation of advanced evasion techniques such as indirect syscalls and sleep obfuscation,” researchers Niraj Shivtarkar and Niraj Shivtarkar said.
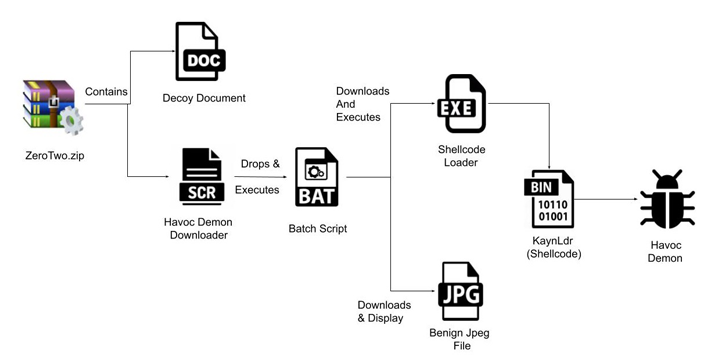
The attack sequence documented by Zscaler begins with a ZIP archive that embeds a decoy document and a screen-saver file that’s designed to download and launch the Havoc Demon agent on the infected host.
Demon is the implant generated via the Havoc Framework and is analogous to the Beacon delivered via Cobalt Strike to achieve persistent access and distribute malicious payloads.
It also comes with a wide variety of features that makes it difficult to detect, turning it into a lucrative tool in the hands of threat actors even as cybersecurity vendors are pushing back against the abuse of such legitimate red team software.
“After the Demon is deployed successfully on the target’s machine, the server is able to execute various commands on the target system,” Zscaler said, adding the server logs the command and its response upon execution. The results are subsequently encrypted and transmitted back to the C2 server.
Havoc has also been employed in connection with a fraudulent npm module dubbed aabquerys that, once installed, triggers a three-stage process to retrieve the Demon implant. The package has since been taken down.
Source: thehackernews.com










