Security researchers have shared a deep dive into the commercial Android spyware called Predator, which is marketed by the Israeli company Intellexa (previously Cytrox).
Predator was first documented by Google’s Threat Analysis Group (TAG) in May 2022 as part of attacks leveraging five different zero-day flaws in the Chrome web browser and Android.
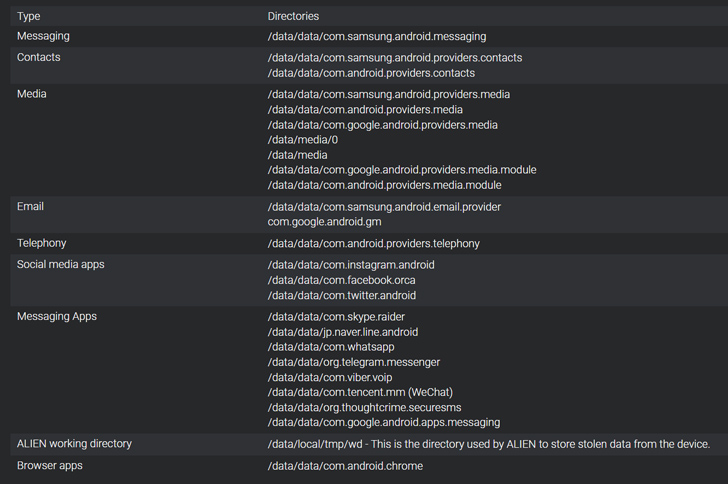
The spyware, which is delivered by means of another loader component called Alien, is equipped to record audio from phone calls and VoIP-based apps as well as gather contacts and messages, including from Signal, WhatsApp, and Telegram.
Its other functionalities allow it to hide applications and prevent applications from being executed upon rebooting the handset.
“A deep dive into both spyware components indicates that Alien is more than just a loader for Predator and actively sets up the low-level capabilities needed for Predator to spy on its victims,” Cisco Talos said in a technical report.
Spyware like Predator and NSO Group’s Pegasus are carefully delivered as part of highly-targeted attacks by weaponizing what are called zero-click exploit chains that typically require no interaction from the victims and allow for code execution and privilege escalation.
“Predator is an interesting piece of mercenary spyware that has been around since at least 2019, designed to be flexible so that new Python-based modules can be delivered without the need for repeated exploitation, thus making it especially versatile and dangerous,” Talos explained.
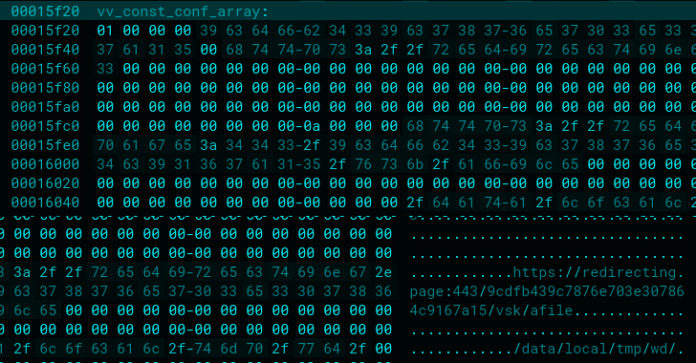
Both Predator and Alien are designed to get around security guardrails in Android, with the latter loaded into a core Android process called Zygote to download and launch other spyware modules, counting Predator, from an external server.
It’s currently not clear how Alien is activated on an infected device in the first place. However, it’s suspected to be loaded from shellcode that’s executed by taking advantage of initial-stage exploits.
“Alien is not just a loader but also an executor — its multiple threads will keep reading commands coming from Predator and executing them, providing the spyware with the means to bypass some of the Android framework security features,” the company said.
The various Python modules associated with Predator make it possible to accomplish a wide array of tasks such as information theft, surveillance, remote access, and arbitrary code execution.
The spyware, which arrives as an ELF binary before setting up a Python runtime environment, can also add certificates to the store and enumerate the contents of various directories on disk if it’s running on a device manufactured by Samsung, Huawei, Oppo, or Xiaomi.
That said, there are still many missing pieces that could help complete the attack puzzle. This comprises a main module called tcore and a privilege escalation mechanism dubbed kmem, both of which have remained elusive to obtain thus far.
Cisco Talos theorized that tcore could have implemented other features like geolocation tracking, camera access, and simulating a shutdown to covertly spy on victims.
The findings come as threat actors’ use of commercial spyware has witnessed a surge in recent years just as the number of cyber mercenary companies supplying these services are on an upward trajectory.
While these sophisticated tools are intended for exclusive use by governments to counter serious crime and combat national security threats, they have also been abused by customers to surveil on dissidents, human rights activists, journalists, and other members of the civil society.
As a case in point, digital rights group Access Now said that it uncovered evidence of Pegasus targeting a dozen people in Armenia – including an NGO worker, two journalists, a United Nations official, and a human rights ombudsperson in Armenia. One of the victims was hacked at least 27 times between October 2020 and July 2021.
“This is the first documented evidence of the use of Pegasus spyware in an international war context,” Access Now said, adding it began an investigation after Apple sent notifications to the individuals in question that they may have been a victim of state-sponsored spyware attacks in November 2021.
There are no conclusive links that connect the spyware use to a specific government agency in either Armenia or Azerbaijan. It’s worth noting that Armenia was outed as a customer of Intellexa by Meta in December 2021 in attacks aimed at politicians and journalists in the nation.
What’s more, cybersecurity company Check Point earlier this year disclosed that various Armenian entities have been infected with a Windows backdoor referred to as OxtaRAT as part of an espionage campaign aligned with Azerbaijani interests.
In a more unusual turn of events, The New York Times and The Washington Post reported this week that the Mexican government may be spying on itself by using Pegasus against a senior official in charge of investigating alleged military abuses.
Mexico is also the first and most prolific user of Pegasus, despite its promises to cease the illegal use of the notorious spyware.
Source: thehackernews.com