A previously unknown advanced persistent threat (APT) is targeting iOS devices as part of a sophisticated and long-running mobile campaign dubbed Operation Triangulation that began in 2019.
“The targets are infected using zero-click exploits via the iMessage platform, and the malware runs with root privileges, gaining complete control over the device and user data,” Kaspersky said.
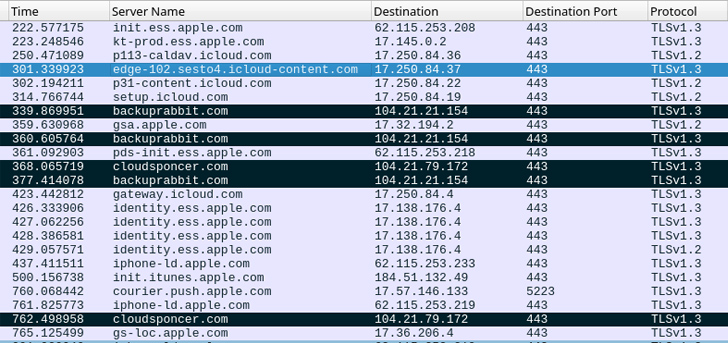
The Russian cybersecurity company said it discovered traces of compromise after creating offline backups of the targeted devices.
The attack chain begins with the iOS device receiving a message via iMessage that contains an attachment bearing the exploit.
The exploit is said to be zero-click, meaning the receipt of the message triggers the vulnerability without requiring any user interaction in order to achieve code execution.
It’s also configured to retrieve additional payloads for privilege escalation and drop a final stage malware from a remote server that Kaspersky described as a “fully-featured APT platform.”
The implant, which runs with root privileges, is capable of harvesting sensitive information and equipped to run code downloaded as plugin modules from the server.
“Further, the spyware also quietly transmits private information to remote servers: microphone recordings, photos from instant messengers, geolocation and data about a number of other activities of the owner of the infected device,” Kaspersky researchers said.
In the final phase, both the initial message and the exploit in the attachment are deleted to erase any traces of the infection.
“The malicious toolset does not support persistence, most likely due to the limitations of the [operating system],” Kaspersky said. “The timelines of multiple devices indicate that they may be reinfected after rebooting.”
The exact scale and scope of the campaign remains unclear, but the company said the attacks are ongoing, with successful infections penetrating devices running iOS 15.7, which was released on September 12, 2022.
It’s currently also not known if the attacks are taking advantage of a zero-day vulnerability – i.e., a flaw discovered by attackers before it’s known to the software vendor – in iOS. The latest version of iOS is 16.5, although Apple also shipped an 15.7.6 update last month.
Kremlin Accuses U.S. of Hacking Thousands of Apple Devices
Coinciding with Kaspersky’s report, Russia’s Federal Security Service (FSB) released an advisory accusing U.S. intelligence agencies of hacking “several thousand” Apple devices belonging to domestic subscribers and foreign diplomats via hitherto unknown pathways as part of a “reconnaissance operation.”
The FSB also claimed the efforts showed “close cooperation” between Apple and the National Security Agency (NSA). No other technical details were provided. Apple, in a statement shared with Reuters, said it has “never worked with any government to insert a backdoor into any Apple product and never will.”
“The U.S. intelligence services have been using IT giants for decades to collect internet users’ personal data without their knowledge,” the Russian Ministry of Foreign Affairs said in a statement. “In this instance, they used the software vulnerabilities of U.S.-made smartphones.”
Kaspersky researcher Ivan Kwiatkowski has since acknowledged the “two sets of activities are in fact related,” citing overlaps in the indicators of compromise (IoCs) released by RU-CERT.
The antimalware vendor further described Operation Triangulation as an “extremely complex, professional targeted cyberattack,” noting it targeted “several dozen iPhones of senior employees.” The real exposure of the espionage campaign is yet to be ascertained.
(The story has been updated after publication to reflect additional information about the attacks and the targets involved.)
Source: thehackernews.com










