Iranian hacker group ‘Mint Sandstorm’ is retaliating against recent attacks on its infrastructure by targeting critical US infrastructure, as recently discovered by cybersecurity researchers at Microsoft’s Threat Intelligence team.
Linked to the IRGC (Islamic Revolutionary Guard Corps) and believed to be working for the Iranian government, the Phosphorous hacking group now operates under the name ‘Mint Sandstorm.’
While apart from this, in 2022, a subgroup of Mint Sandstorm shifted their focus from surveillance to launching direct attacks on crucial US infrastructure.
These attacks on US infrastructure are believed to be a retaliatory response by Iran, attributing recent attacks on their own infrastructure to the US and Israel.
In June 2021, Iran’s railway system was targeted in a destructive attack, followed by a cyberattack that caused a severe blackout at Iranian gas stations in October of the same year.
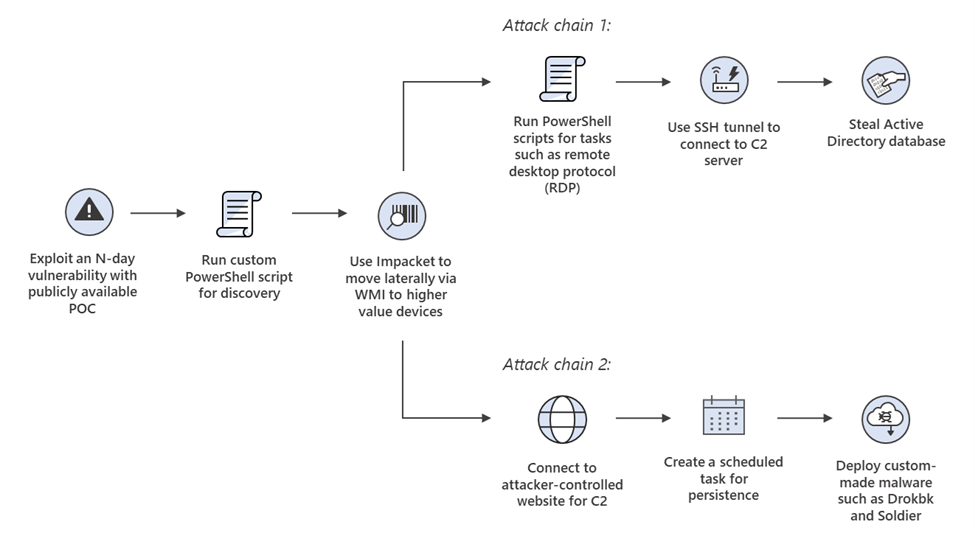
Attack Chain
Microsoft believes an increase in cyberattacks is due to the Iranian government’s loosened hold and restrictions on state-sponsored threat actors offering more freedom.
This follows the sanctioning of individuals and entities affiliated with the IRGC by OFAC last year.
The newly identified subgroup of Mint Sandstorm frequently utilizes proof-of-concept exploits and N-day exploits, including known vulnerabilities such as Log4Shell, in their cyberattacks.
The hackers use a custom PowerShell script to gather information on the targeted network before using the Impacket framework to move laterally and choose between two attack chains.
The hackers’ two attack chains include stealing the Windows Active Directory database to obtain credentials for further intrusion and deploying custom backdoor malware to maintain persistence and deploy additional payloads.
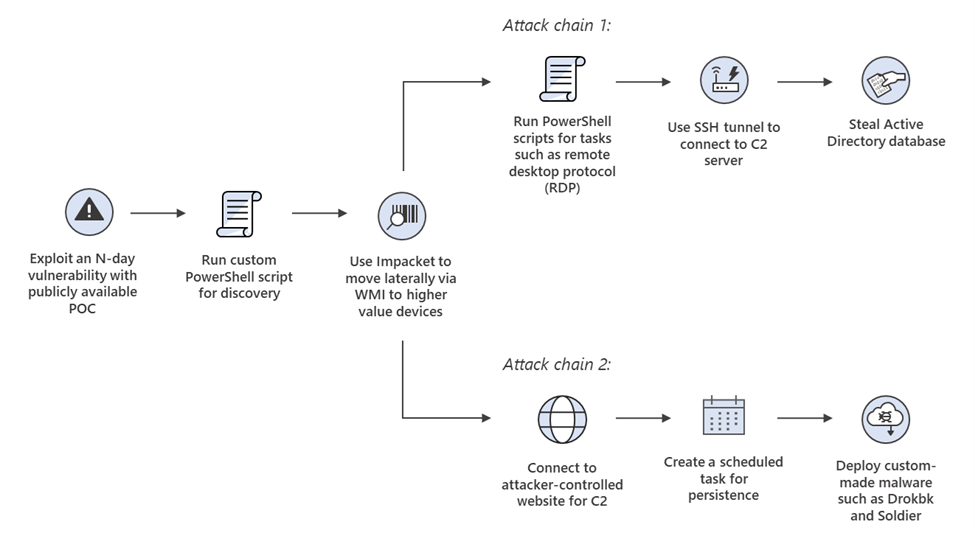
The .NET backdoor malware Drokbk and Soldier fetch a list of command and control server addresses from a GitHub repository controlled by the attacker.
While the former works as an installer, the latter can download extra payloads and remove itself from the system.
Alongside using exploits to breach networks, the attackers also conducted low-volume phishing attacks, including links to OneDrive accounts with spoofed PDFs containing Middle East-related security or policy information, targeting a few victims.
The phishing attacks used malicious PDFs containing links for a Word template that executed a payload on the device through template injection.
The CharmPower PowerShell post-exploitation framework was deployed for persistence and executing additional commands.
The observed capabilities in the cyberattacks attributed to the Mint Sandstorm subgroup are alarming, as they allow for concealed C2 communication, system persistence, and a wide range of post-compromise tools, with initial access potentially leading to further behaviors that could compromise the confidentiality, integrity, and availability of a system.
Attack Surface Reduction Rules
Here below, we have mentioned the attack surface reduction rules recommended by Microsoft to prevent the execution of non-compliant executables:-
- Executable files must meet a prevalence, age, or trusted list criterion before they can be executed.
- Disallow the creation of executable content by Office applications.
- PSExec and WMI-based process creation should be blocked.
Since the vulnerabilities are a primary means of entry into corporate networks for these threat actors.
Struggling to Apply The Security Patch in Your System? –
Try All-in-One Patch Manager Plus
Source: gbhackers.com