Guardio Labs discovered a Chrome Extension that promotes rapid access to fake ChatGPT functionality capable of stealing Facebook accounts and establishing hidden account backdoors.
Using a maliciously imposed Facebook app “backdoor” that grants the threat actors super-admin powers stands out.
“By hijacking high-profile Facebook business accounts, the threat actor creates an elite army of Facebook bots and a malicious paid media apparatus,” Guardio Labs reports.
“This allows it to push Facebook paid ads at the expense of its victims in a self-propagating worm-like manner.”
Tactics Employed By This Powerful Stealer
The Guardio Labs research team discovered a new version of the malicious fake ChatGPT browser extension. This time, it has been updated with a frightening method to take control of your Facebook accounts and a sophisticated worm-like way for spreading.
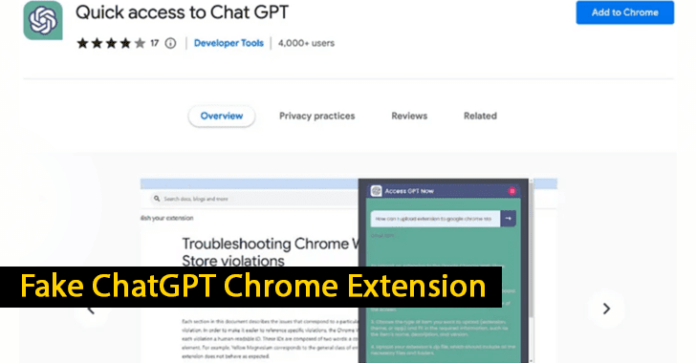
On Facebook-sponsored posts, the malicious stealer extension dubbed “Quick access to Chat GPT” is advertised as a fast way to launch ChatGPT straight from your browser.
Reports say although the extension gives you that (by merely connecting to the official ChatGPT’s API), it also gathers all the data it can from your browser, steals cookies from allowed active sessions to any service you have, and uses targeted methods to take over your Facebook account.
Using two fake Facebook applications, portal and msg kig, backdoor access is maintained, and complete control of the target profiles is attained. Adding apps to Facebook accounts is a fully automated procedure.
“With this approach, the campaign can continue propagating with its army of hijacked Facebook bot accounts, publishing more sponsored posts and other social activities on behalf of its victim’s profiles and spending business account money credits!” Guardio Labs.
After you click on the extension icon after it has been installed, a small popup window with a prompt to ask ChatGPT whatever you want appears. This is precisely what the extension promises.
As a result, it can send any request to any other service, just as if the browser owner were the one requesting the first place. This is important since, in most circumstances, the browser already has an active and authenticated session with nearly all your daily services, such as Facebook.
This enables the extension to utilize Meta’s Graph API for developers, giving the threat actor rapid access to your details and the ability to perform activities on your behalf from within your Facebook account via straightforward API calls.
“Not only this malicious extension is free-roaming on the official Chrome store, but it is also abusing Facebook’s official applications API in a way that should have triggered policy enforcers’ attention already,” Guardio Labs.
Reports state that since its appearance on March 3, 2023, this extension has been installed by more than 2000 users daily. As a result, each person has their Facebook account stolen. However, this is likely not the only harm.
The extension has since been removed from Chrome’s store due to Guardio’s Google report on this malicious extension.
Hence, we need to be more cautious even when doing regular, casual browsing. For example, avoid clicking on the first search result, and always be careful to only click on sponsored links and posts if you are confident of their source.
Network Security Checklist – Download Free E-Book
Related Read
Source: gbhackers.com