In a recent analysis, MQsTTang, a newly designed custom backdoor, has been scrutinized by ESET researchers. After a thorough investigation, the source of this malware has been attributed to the infamous Mustang Panda APT group by the experts.
Tracing back to early January 2023, this ongoing campaign is attributed to the newly discovered backdoor. Customized versions of the PlugX malware are the weapon of choice for the notorious Mustang Panda APT group (aka TA416 and Bronze President), recognized for their worldwide data theft attacks.
This group operates as an advanced persistent threat (APT), with the intent to steal sensitive information from targeted organizations.
The latest malware, MQsTTang, introduced by Mustang Panda APT group, seems to be an original creation, not based on any prior malware. This suggests that the hackers designed it to bypass detection and restrict attribution to their group.
Distribution
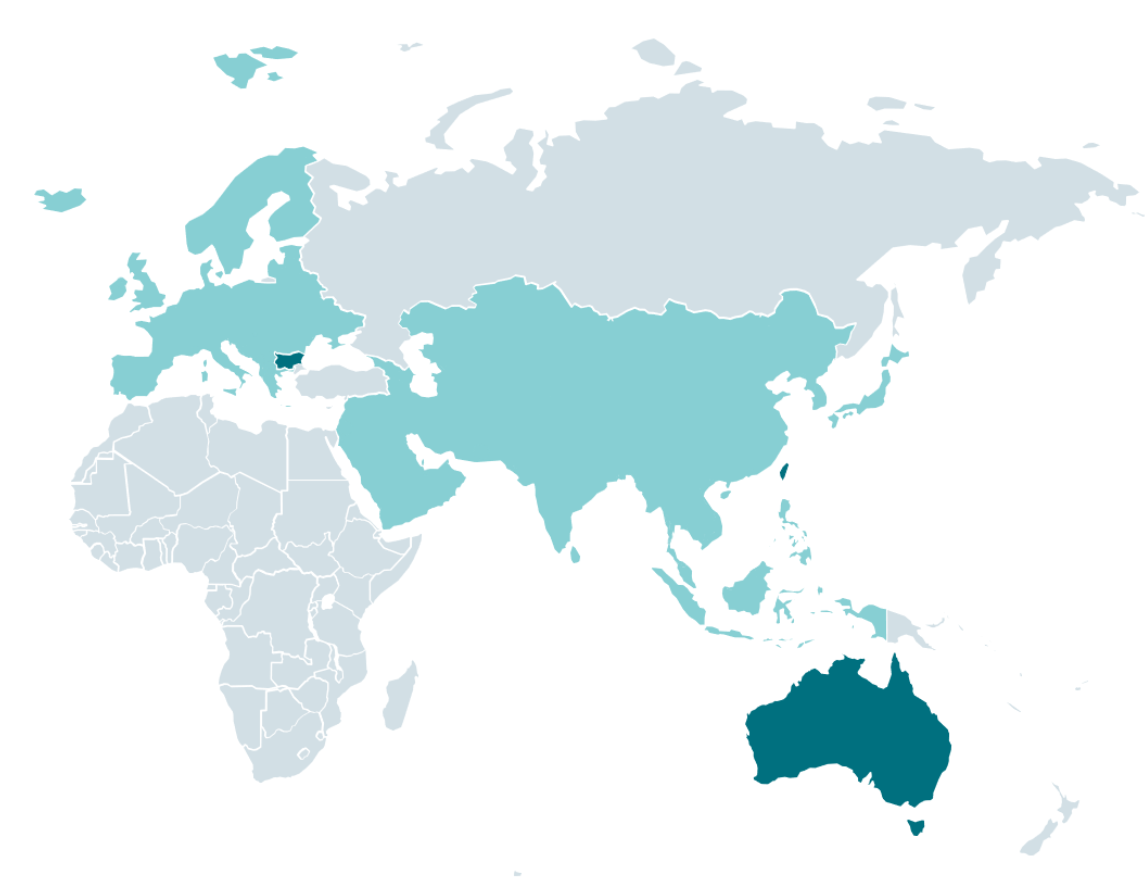
With its primary focus on Taiwan and Ukraine, the ongoing campaign targets government and political organizations in Europe and Asia. It is pertinent to note that these regions have been on the radar of many notorious hacking groups for their geopolitical importance.
Spear-phishing emails are the preferred mode for the distribution of the malware, while the payloads are downloaded from GitHub repositories created by a user affiliated with past campaigns of the Mustang Panda.
The malware in question is compressed in RAR archives and is executable once unzipped, and its file names have a distinctive diplomacy theme.
Attack chain
According to ESET Report, MQsTTang is a “barebones” backdoor that provides the threat actor with remote command execution capabilities on the victim’s computer and allows them to receive the output of the commands.
The malware duplicates itself upon execution and includes a command-line argument that initiates several operations. Persistence is achieved by creating a new registry key under the following path to initiate the malware during system startup:-
- HKCUSoftwareMicrosoftWindowsCurrentVersionRun
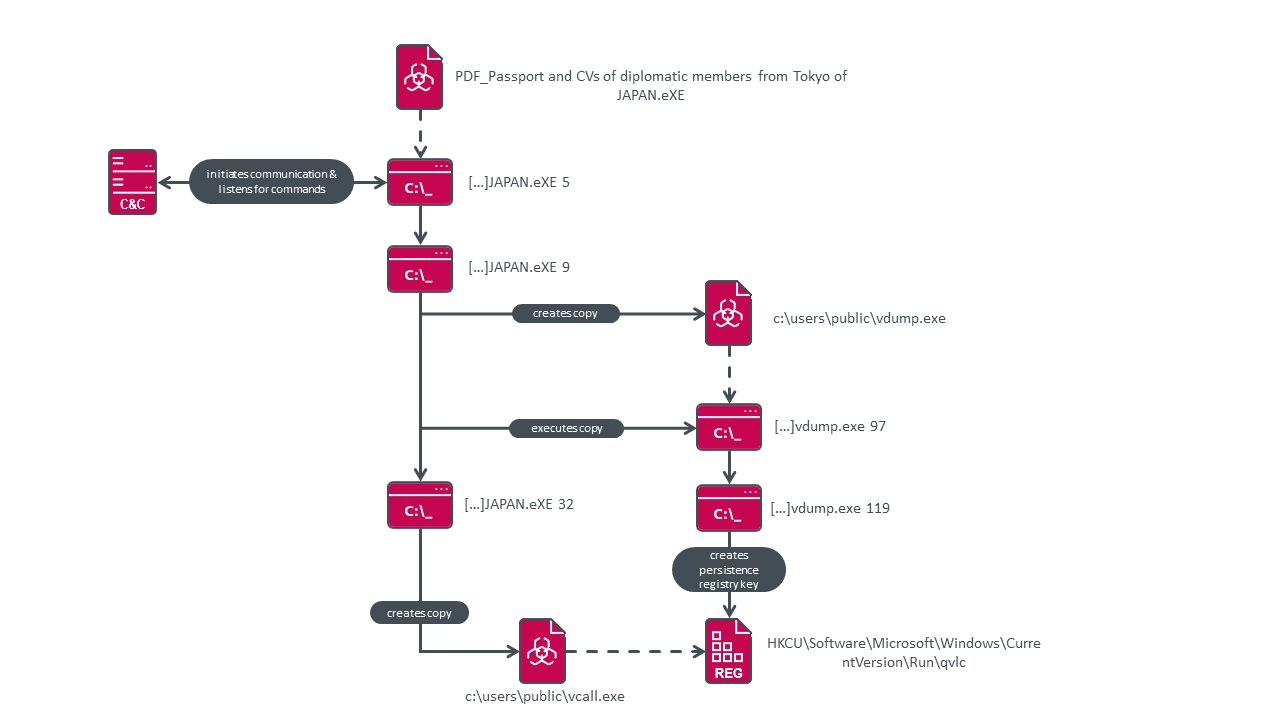
There is only one task that is executed after rebooting, and that is the C2 communication task. The novel backdoor has an atypical trait in that it utilizes the MQTT protocol for facilitating communication between the command and control server.
The malware is imbued with an inherent ability to withstand command and control (C2) takedowns and evade detection by defenders.
This is owing to the employment of MQTT, which facilitates communication through a broker and keeps the attacker’s infrastructure hidden. This makes it a less detectable choice compared to other commonly used C2 protocols that are frequently scrutinized by defenders.
In order to remain undetected, the MQsTTang malware employs a mechanism to detect the presence of debugging or monitoring tools on the host system. If any such tools are identified, the malware adapts its behavior to avoid detection.
Analysts at Trend Micro recently detected another instance of a Mustang Panda operation that spanned from March to October 2022.
It is currently uncertain whether the MQsTTang malware will be incorporated into the long-term arsenal of the group responsible for its development or if it was created solely for a specific operation.
Indicators of Compromise
Files
| SHA-1 | Filename | Detection | Description |
|---|---|---|---|
| A1C660D31518C8AFAA6973714DE30F3D576B68FC | CVs Amb.rar | Win32/Agent.AFBI | RAR archive used to distribute MQsTTang backdoor. |
| 430C2EF474C7710345B410F49DF853BDEAFBDD78 | CVs Amb Officer PASSPORT Ministry Of Foreign Affairs.exe | Win32/Agent.AFBI | MQsTTang backdoor. |
| F1A8BF83A410B99EF0E7FDF7BA02B543B9F0E66C | Documents.rar | Win32/Agent.AFBI | RAR archive used to distribute MQsTTang backdoor. |
| 02D95E0C369B08248BFFAAC8607BBA119D83B95B | PDF_Passport and CVs of diplomatic members from Tokyo of JAPAN.eXE | Win32/Agent.AFBI | MQsTTang backdoor. |
| 0EA5D10399524C189A197A847B8108AA8070F1B1 | Documents members of delegation diplomatic from Germany.Exe | Win32/Agent.AFBI | MQsTTang backdoor. |
| 982CCAF1CB84F6E44E9296C7A1DDE2CE6A09D7BB | Documents.rar | Win32/Agent.AFBI | RAR archive used to distribute MQsTTang backdoor. |
| 740C8492DDA786E2231A46BFC422A2720DB0279A | 23 from Embassy of Japan.exe | Win32/Agent.AFBI | MQsTTang backdoor. |
| AB01E099872A094DC779890171A11764DE8B4360 | BoomerangLib.dll | Win32/Korplug.TH | Known Mustang Panda Korplug loader. |
| 61A2D34625706F17221C1110D36A435438BC0665 | breakpad.dll | Win32/Korplug.UB | Known Mustang Panda Korplug loader. |
| 30277F3284BCEEF0ADC5E9D45B66897FA8828BFD | coreclr.dll | Win32/Agent.ADMW | Known Mustang Panda Korplug loader. |
| BEE0B741142A9C392E05E0443AAE1FA41EF512D6 | HPCustPartUI.dll | Win32/Korplug.UB | Known Mustang Panda Korplug loader. |
| F6F3343F64536BF98DE7E287A7419352BF94EB93 | HPCustPartUI.dll | Win32/Korplug.UB | Known Mustang Panda Korplug loader. |
| F848C4F3B9D7F3FE1DB3847370F8EEFAA9BF60F1 | libcef.dll | Win32/Korplug.TX | Known Mustang Panda Korplug loader. |
Network Security Checklist – Download Free E-Book
Source: gbhackers.com