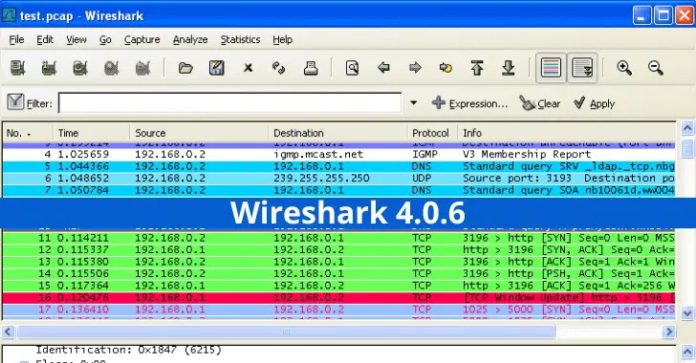
Wireshark is a free and open-source network packet analyzer used by people worldwide. It has a wide range of uses when it comes to packet analysis.
The original name of Wireshark is “Ethreal” released by Gerald Combs in late 1997.
With the current release, the latest version of Wireshark is 4.0.6. However, as stated by Wireshark, the official 32-bit Windows packages are no longer shipped.
For users who wish to use Wireshark in 32-bit Windows, it is recommended to go with the latest 3.6 release.
Vulnerabilities Fixed in Wireshark 4.0.6
Wireshark has fixed 9 existing vulnerabilities in the new release.
An attacker can exploit this vulnerability by sending a specially crafted payload file. When opened by Wireshark, this file can crash the application and result in potential code execution.
- CVE-2023-2857 – Heap buffer overflow vulnerability in BLF reader
An attacker can exploit this vulnerability by sending a maliciously crafted BLF file that affects the blf_pull_logcontainer_into_memory() function. This can result in arbitrary code execution.
- GDSDB dissector infinite loop
An attacker can exploit this vulnerability by sending a malicious packet which results in excessive CPU resource usage by Wireshark,
- CVE-2023-2858 – Heap Buffer Overflow in nstrace_read_v10 Function
An attacker can exploit this vulnerability by sending a malicious packet file that executes an arbitrary code or results in a DoS for Wireshark that crashes the application.
- CVE-2023-2856 – Stack Buffer Overflow in parse_vms_packet Function
An attacker can exploit this vulnerability by sending a malicious file to wireshark that is read by the parse_vms_packet function resulting in the crash of Wireshark. Alternatively, it can also result in arbitrary code.
- CVE-2023-2854 – Heap Buffer Overflow blf_read_apptextmessage Function
This vulnerability exists in the blf_read_apptextmessage function of the Wireshark BLF plugin, which can be exploited by sending a crafted string resulting in arbitrary code execution.
The RTPS (Real-Time Publish-Subscribe) packet in the Wireshark version 4.0.5 and earlier does not validate the length in the rtps_util_add_type_library_type.
An attacker can exploit this by sending a large file to this function resulting in a heap buffer overflow vulnerability that can also lead to code execution.
The global buffer conf_phasor_type has an out-of-bounds read capability that does not validate the length of the IEEE-C37.118 packet sent by an attacker, resulting in a heap-based buffer overflow and can lead to arbitrary code execution.
- XRA dissector infinite loop
An attacker can exploit this vulnerability by sending a malicious packet which, when read by Wireshark, can result in a crash of the application.
Along with these vulnerabilities, several bugs in the Wireshark application have also been fixed in the recent release.
Protocol update
In addition to these bugs and vulnerability fixes, Wireshark has also added some protocol support. The current version supports protocols like,
- batadv
- BFCP
- CommunityID
- COSE
- GDSDB
- H.265
- HTTP
- ILP
- ISAKMP
- MSMMS
- NNTP
- NR RRC
- NTLMSSP
- QUIC
- RTPS
- SPNEGO
- Synphasor
- TCP
- UDS
- ULP
- USB HID
- and XRA
For more information on the release, visit the Wireshark 4.0.6 release notes page.
Shut Down Phishing Attacks with Device Posture Security – Download Free E-Book
Source: gbhackers.com