A new malware strain known as the cybersecurity analysts at Trustwave SpiderLabs recently discovered Rilide. This new malware is specifically designed to attack web browsers that are built on the Chromium platform, including:-
- Google Chrome
- Microsoft Edge
- Brave
- Opera
Trustwave SpiderLabs researchers have discovered that Rilide camouflages itself as a legit Google Drive extension to evade detection and leverages inherent Chrome features for malicious purposes.
Abilities of Rilide
There is a multitude of malicious activities that can be carried out by threat actors using Rilide malware, including the following:-
- Monitoring browsing history
- Taking screenshots
- Injecting malicious scripts
Trustwave SpiderLabs has previously encountered other instances of malware exploiting harmful browser extensions, and Rilide is no exception.
Malicious Campaigns
Rilide’s unique capability to exploit counterfeit dialogs is what sets it apart from other malware. These dialogs are then used to trick users into disclosing their two-factor authentication (2FA) information, which it then employs to steal cryptocurrencies covertly.
Two malicious campaigns were discovered by SpiderLabs, designed to install the Rilide browser extension on the victim’s device.
Here below, we have mentioned campaigns:-
- Campaign 1: Ekipa RAT Installing Rilide Stealer
- Campaign 2: Aurora Stealer Abusing Google Ads
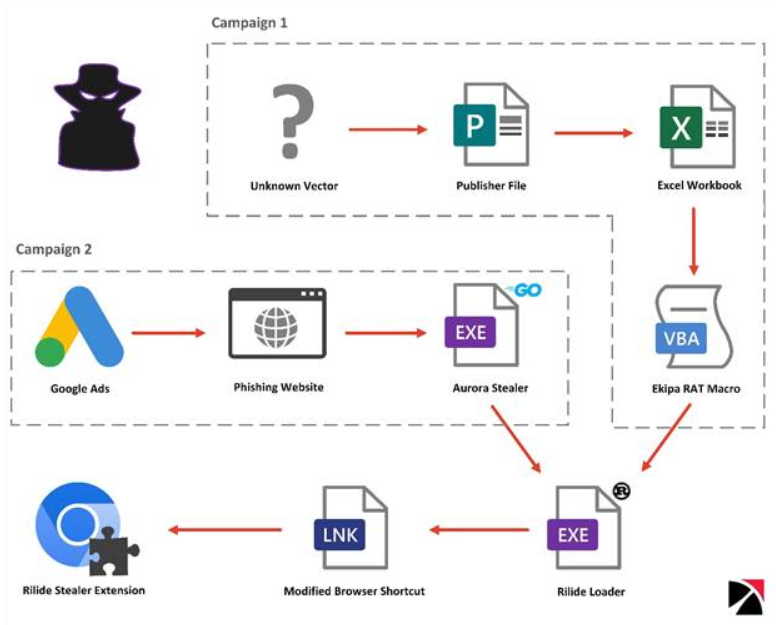
There are two methods of loading the extension through the Rust loader:-
- One is done via Google Ads
- Other is done via Aurora Steale
To distribute the malicious extension, one of them uses the Ekipa RAT. Trustwave reports that there is an overlap between the malware and similar extensions that are sold to cybercriminals, although the origin of the malware is unknown.
Furthermore, some parts of its code have been leaked on an underground forum following a dispute over hackers’ overpayment that has not been resolved.
An Extension Like Leech
A malicious extension is dropped on the compromised system by Rilide’s loader through modifications to the web browser shortcut files.
When the malware is executed, it executes a script that attaches a listener to the process. Threat actors usually use a listener like this to detect when a victim switches tabs, receives content from a website, or loads a page.
Furthermore, the site’s current URL is checked against the list of targets available on the C2 server to determine if it matches.
The extension will load additional scripts when a match is found, which will then be injected into the webpage to steal information from the victim. While the data targeted is mainly related to:-
- Cryptocurrencies
- Email account credentials
- Bank wallets
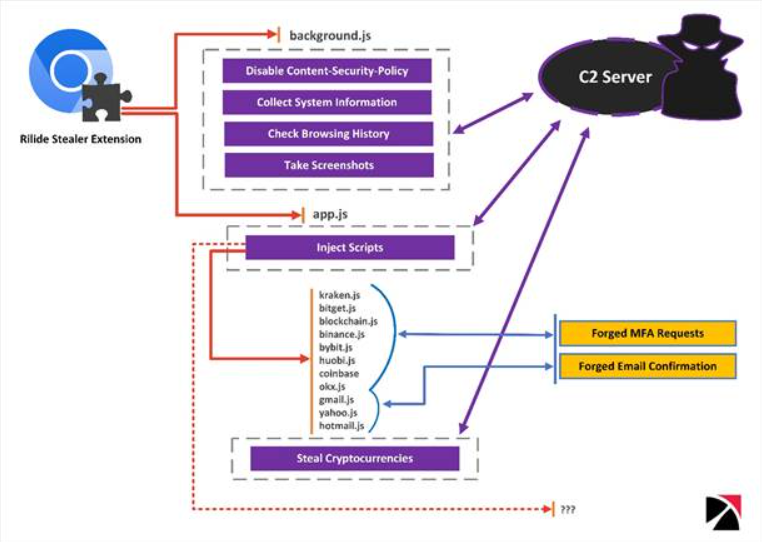
The malicious extension not only bypasses the ‘Content Security Policy’ (CSP) feature of a web browser to load external resources that are usually blocked freely, but it also can capture screenshots and exfiltrate browsing history is then transmitted to the attacker’s command-and-control (C2) server.
Bypassing 2FA
Rilide’s forging system is triggered when a victim tries to withdraw cryptocurrency from an exchange service targeted by malware. At this point, the malicious script is injected in the background, allowing the malware to process the request automatically.
To complete the withdrawal process, Rilide uses the code entered by the user on the fake dialog. Once done, the withdrawal amount is automatically transferred to the threat actor’s wallet address.
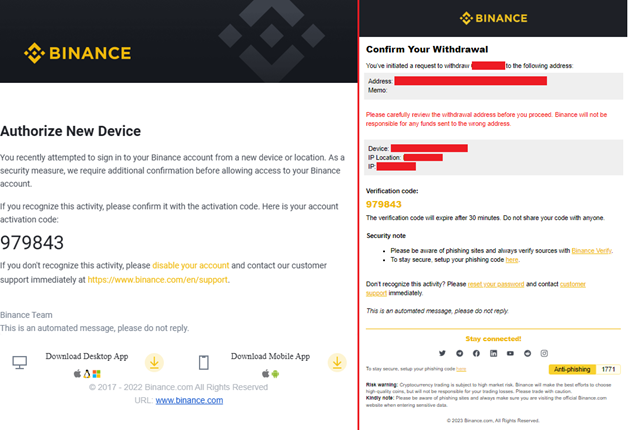
If the user accesses their mailbox through the same web browser, Rilide replaces email confirmations, including the withdrawal request email, which is substituted with a fake device authorization request.
The advancement of Rilide highlights the increasingly sophisticated nature of malicious browser extensions, which now feature live monitoring and automated systems for stealing money.
Although the enforcement of Manifest v3 may make it more challenging for threat actors to operate, it is improbable to resolve the problem entirely since most of Rilide’s functions will still be accessible.
Struggling to Apply The Security Patch in Your System? – Try All-in-One Patch Manager Plus
Related Read:
Source: gbhackers.com











