A novel credential-stealing malware called Zaraza bot is being offered for sale on Telegram while also using the popular messaging service as a command-and-control (C2).
“Zaraza bot targets a large number of web browsers and is being actively distributed on a Russian Telegram hacker channel popular with threat actors,” cybersecurity company Uptycs said in a report published last week.
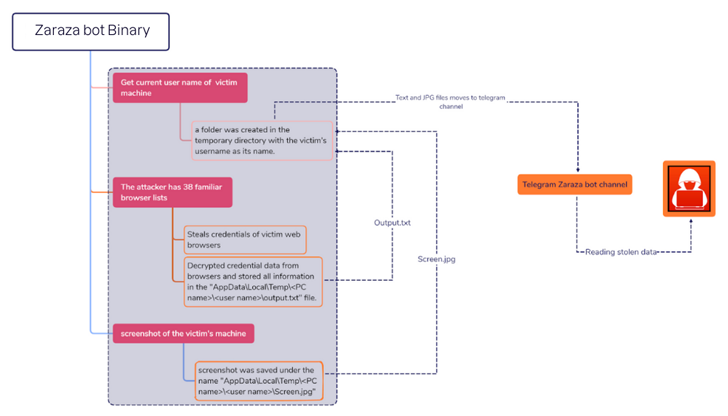
“Once the malware infects a victim’s computer, it retrieves sensitive data and sends it to a Telegram server where the attackers can access it immediately.”
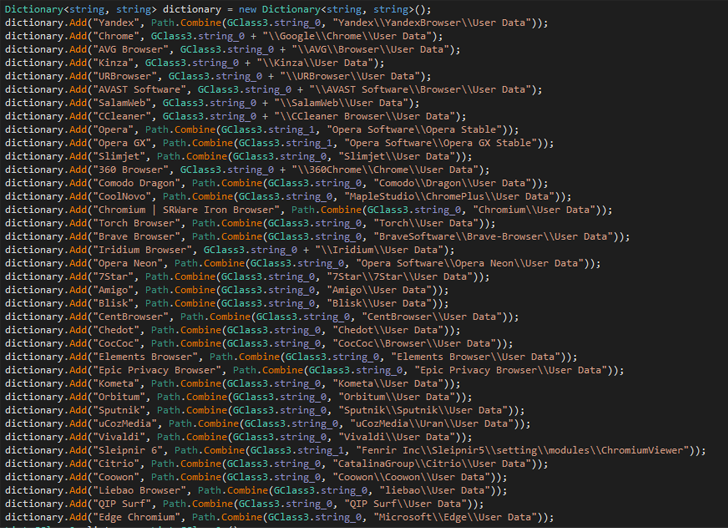
A 64-bit binary file compiled using C#, Zaraza bot is designed to target as many as 38 different web browsers, including Google Chrome, Microsoft Edge, Opera, AVG Browser, Brave, Vivaldi, and Yandex. It’s also equipped to capture screenshots of the active window.
It’s the latest example of malware that’s capable of capturing login credentials associated with online bank accounts, cryptocurrency wallets, email accounts, and other websites deemed of value to the operators.
Stolen credentials pose a serious risk as they not only allow threat actors to gain unauthorized access to victims’ accounts, but also conduct identity theft and financial fraud.
Evidence gathered by Uptycs points to Zaraza bot being offered as a commercial tool for other cybercriminals for a subscription. It’s currently not clear how the malware is propagated, but information stealers have typically leveraged several methods such as malvertising and social engineering in the past.
The findings come as eSentire’s Threat Response Unit (TRU) disclosed a GuLoader (aka CloudEyE) campaign targeting the financial sector via phishing emails by employing tax-themed lures to deliver information stealers and remote access trojans (RATs) like Remcos RAT.
The development also follows a spike in malvertising and search engine poisoning techniques to distribute a growing number of malware families by enticing users searching for legitimate applications into downloading fake installers containing stealer payloads.
Russian cybersecurity firm Kaspersky, in a new analysis, revealed the use of trojanized cracked software downloaded from BitTorrent or OneDrive to deploy CueMiner, a .NET-based downloader that acts as a conduit to installer a cryptocurrency miner known as SilentCryptoMiner.
To mitigate risks stemming from stealer malware, it’s recommended that users enable two-factor authentication (2FA) and apply software and operating systems updates as and when they become available.
Source: thehackernews.com