The North Korean state-sponsored threat actor known as Kimsuky has been discovered using a new reconnaissance tool called ReconShark as part of an ongoing global campaign.
“[ReconShark] is actively delivered to specifically targeted individuals through spear-phishing emails, OneDrive links leading to document downloads, and the execution of malicious macros,” SentinelOne researchers Tom Hegel and Aleksandar Milenkoski said.
Kimsuky is also known by the names APT43, ARCHIPELAGO, Black Banshee, Nickel Kimball, Emerald Sleet (previously Thallium), and Velvet Chollima.
Active since at least 2012, the prolific threat actor has been linked to targeted attacks on non-governmental organizations (NGOs), think tanks, diplomatic agencies, military organizations, economic groups, and research entities across North America, Asia, and Europe.
The latest intrusion set documented by SentinelOne leverages geopolitical themes related to North Korea’s nuclear proliferation to activate the infection sequence.
“Notably, the spear-phishing emails are made with a level of design quality tuned for specific individuals, increasing the likelihood of opening by the target,” the researchers said. “This includes proper formatting, grammar, and visual clues, appearing legitimate to unsuspecting users.”
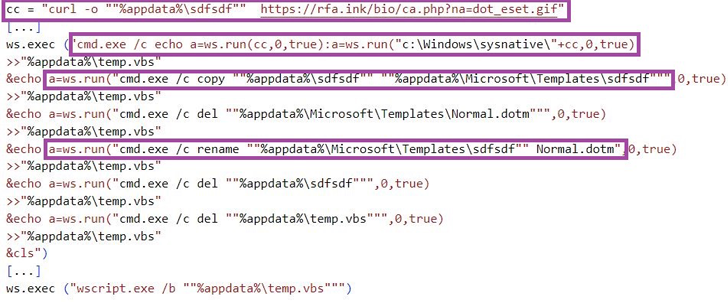
These messages contain links to booby-trapped Microsoft Word documents hosted on OneDrive to deploy ReconShark, which chiefly functions as a recon tool to execute instructions sent from an actor-controlled server. It’s also an evolution of the threat actor’s BabyShark malware toolset.
“It exfiltrates system information to C2 server, maintains persistence on the system, and waits for further instruction from the operator,” Palo Alto Networks Unit 42 said in its analysis of BabyShark in February 2019.
ReconShark is specifically designed to exfiltrate details about running processes, deployed detection mechanisms and hardware information, suggesting that data gathered from the tool is used to carry out “precision attacks” involving malware tailored to the targeted environment in a manner that sidesteps detection.
The malware is also capable of deploying additional payloads from the server based on “what detection mechanism processes run on infected machines.”
The findings add to growing evidence that the threat actor is actively shifting its tactics to get a foothold on compromised hosts, establish persistence, and stealthily gather intelligence for extended periods of time.
“The ongoing attacks from Kimsuky and their use of the new reconnaissance tool, ReconShark, highlight the evolving nature of the North Korean threat landscape,” SentinelOne said.
Source: thehackernews.com










