An open source adversary-in-the-middle (AiTM) phishing kit has found a number of takers in the cybercrime world for its ability to orchestrate attacks at scale.
The Microsoft Threat Intelligence team is tracking the threat actor behind the development of the kit under its emerging moniker DEV-1101.
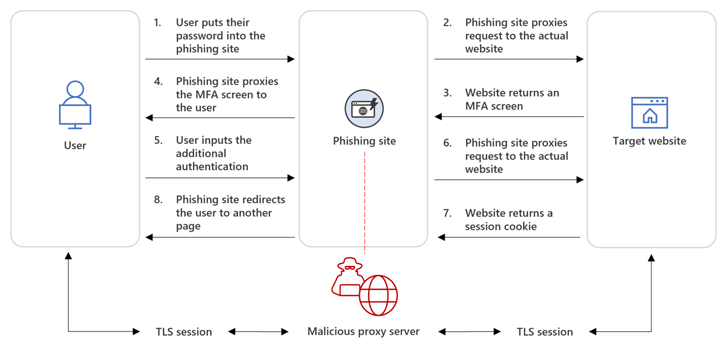
An AiTM phishing attack typically involves a threat actor attempting to steal and intercept a target’s password and session cookies by deploying a proxy server between the user and the website.
Such attacks are more effective owing to their ability to circumvent multi-factor authentication (MFA) protections, specifically time-based one-time passwords (TOTPs).
DEV-1101, per the tech giant, is said to be the party behind several phishing kits that can be purchased or rented by other criminal actors, thereby reducing the effort and resources required to launch a phishing campaign.
“The availability of such phishing kits for purchase by attackers is part of the industrialization of the cybercriminal economy and lowers the barrier of entry for cybercrime,” Microsoft said in a technical report.
The service-based economy that fuels such offerings can also result in double theft, wherein the stolen credentials are sent to both the phishing-as-a-service provider as well as their customers.
The open source kit from DEV-1101 comes with features that make it possible to set up phishing landing pages mimicking Microsoft Office and Outlook, not to mention manage campaigns from mobile devices and even use CAPTCHA checks to evade detection.
The service, since its debut in May 2022, has undergone several enhancements, chief among them being the ability to manage servers running the kit through a Telegram bot. It currently has a price tag of $300 for a monthly licensing fee, with VIP licenses costing $1,000.
Microsoft said it has detected numerous high-volume phishing campaigns spanning millions of phishing emails per day from various actors that leverage the tool.
This includes an activity cluster dubbed DEV-0928 that Redmond described as one of “DEV-1101’s more prominent patrons” and which has been linked to a phishing campaign comprising over one million emails since September 2022.
The attack sequence commences with document-themed email messages containing a link to a PDF file, that when clicked, directs the recipient to a login page that masquerades as Microsoft’s sign-in portal, but not before urging the victim to complete a CAPTCHA step.
“Inserting a CAPTCHA page into the phishing sequence could make it more difficult for automated systems to reach the final phishing page, while a human could easily click through to the next page,” Microsoft said.
Although these AiTM attacks are designed to bypass MFA, it’s crucial that organizations adopt phishing-resistant authentication methods, such as using FIDO2 security keys, to block suspicious login attempts.
Source: thehackernews.com