The security analysts at Akamai recently identified a new botnet called HinataBot, based on Golang. Apart from this, HinataBot has been observed exploiting the already-known security flaws in routers and servers to gain unauthorized access to launch DDoS attacks.
At the beginning of the year, researchers uncovered this new botnet that had been operating for quite some time. While it has been discovered that HinataBot targets the following routers and servers:-
- Realtek SDK devices
- Huawei HG532 routers
- Hadoop YARN servers
Exploiting Known Flaws
In the malware binaries, a character from the popular anime series, Naruto appears to have been given a name by the malware author.
Akamai’s SIRT found HinataBot within HTTP and SSH honeypots exploiting the old known vulnerabilities, and here below we have mentioned them:-
- CVE-2014-8361
- CVE-2017-17215
Distribution
As early as mid-January 2023, Mirai binaries were distributed by HinataBot’s operators, which was the first time it appeared.
The HinataBot Botnet underwent active development with the addition of several improvements and new features as recently as March 2023. While this has been confirmed by the cybersecurity researchers at Akamai during the analysis of active campaigns from which they caught multiple samples of the botnet.
Several attacks have taken place as a result of unpatched vulnerabilities and weak credentials, which represent an easy entry point for the threat actors without using any sophisticated tactics.
Since December 2022, the HinataBot botnet has been active. As of January 11, 2023, they began using their own custom malware to conduct the attacks, following the use of a generic Go-based Mirai variant as the initial attack.
The experts have not yet observed a real-life attack since the C2 is currently down. The trackers are not yet connected. However, the process of doing so is currently underway.
The primary goal of the researchers is to be able to observe closely if they become active again in the future.
Massive DDoS Capability
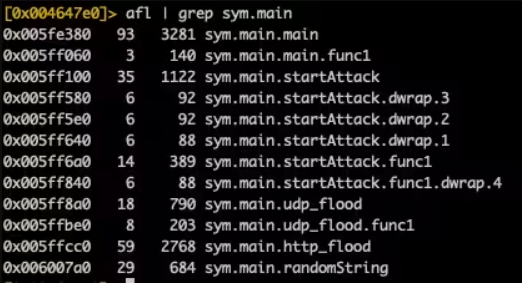
A number of functions that were particularly notable came to light during the analysis. Their attention was immediately caught by three distinct attack functions, and here they are mentioned below:-
- sym.main.startAttack
- sym.main.http_flood
- sym.main.udp_flood
Infection scripts and RCE payloads for known vulnerabilities are used in order to distribute malware through brute-force attacks on SSH endpoints.
Once a device is infected, the malware quietly runs, waiting for command and control server instructions to be executed.
In order to observe HinataBot in action and infer the malware’s attack capabilities, Akamai’s analysts designed their own C2 and interacted with simulated infections.
Here below, we have mentioned the floods that are supported by older versions of HinataBot:-
While in the case of the new version of HinataBot, only HTTP and UDP floods are supported. But, the botnet is capable of performing very powerful DDoS attacks even with just two attack modes.
Taking into consideration that there can be 10,000 bots in an attack, a UDP flood may reach a peak of over 3.3 Tbps, making it a powerful attack. There is a difference between the HTTP attack command and the UDP attack command.
In both cases, 512 workers are created for a worker pool and assigned a fixed duration for a defined period to send data packets to all predefined targets.
There is a range of 484 to 589 bytes in the size of an HTTP packet. A large number of null bytes are included in the UDP packets generated by HinataBot, which can overwhelm the target with a significant amount of traffic.
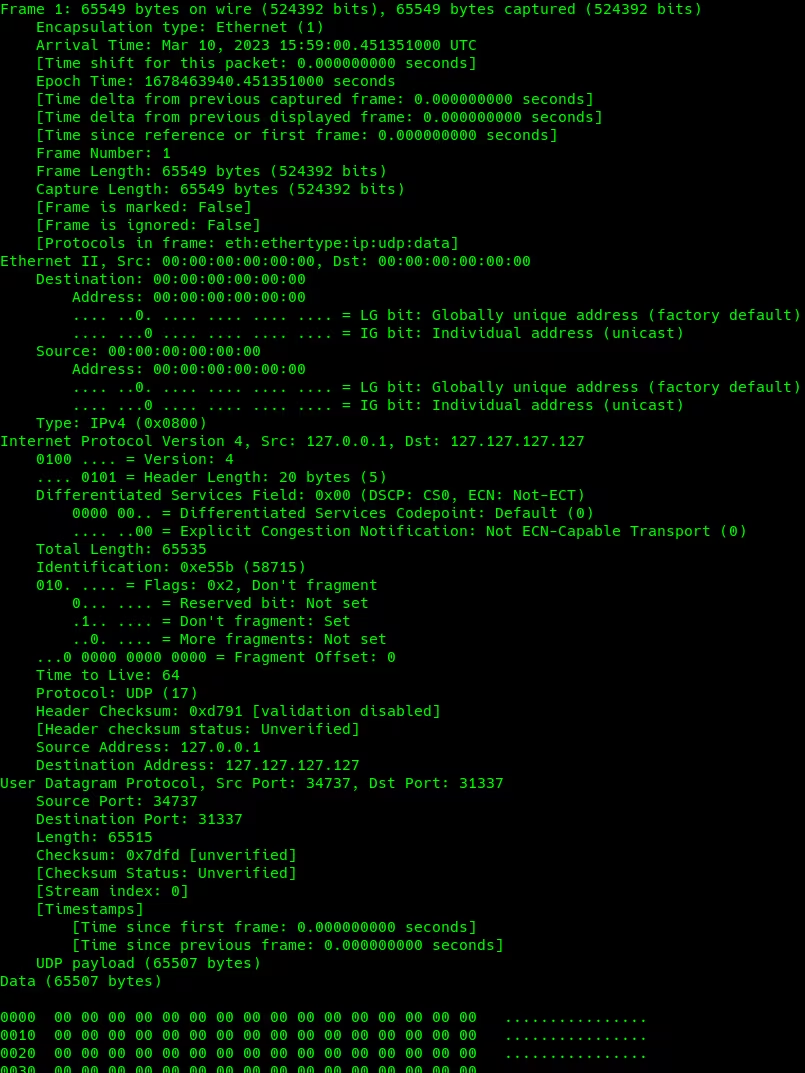
The two methods utilize different approaches to achieve the same result; HTTP floods generate heavy traffic to the website, whereas UDP floods send garbage to the target.
It generated 20,430 requests for a total size of 3.4MB for the HTTP attack, Akamai benchmarked the botnet in 10-second attacks for HTTP and UDP. The UDP flood generated a total of 421 MB of data, about 6,733 packages.
There is still room for improvement in HinataBot Botnet, and it is likely to implement additional exploits and expand its targeting capabilities at any time.
Building Your Malware Defense Strategy – Download Free E-Book
Source: gbhackers.com