Trend Micro researchers have recently demonstrated that malware and malicious scripts can be hosted and distributed within GitHub Codespaces by malicious actors through the use of port forwarding functionality.
GitHub Codespaces allows developers to quickly set up a workspace and start coding directly within minutes in a web browser, without having to worry about setup, configuration, and dependencies.
This makes it much easier and faster to get started with a project, and it also reduces the need for developers to switch between different development environments.
Malware Server Hosted on GitHub Codespaces
GitHub Codespaces provide developers with cloud-hosted development environments that are easily accessible and can be quickly configured.

This makes them an attractive target for malicious actors who can use them to quickly set up malicious web servers, which can be used to distribute malware or other malicious content without detection.
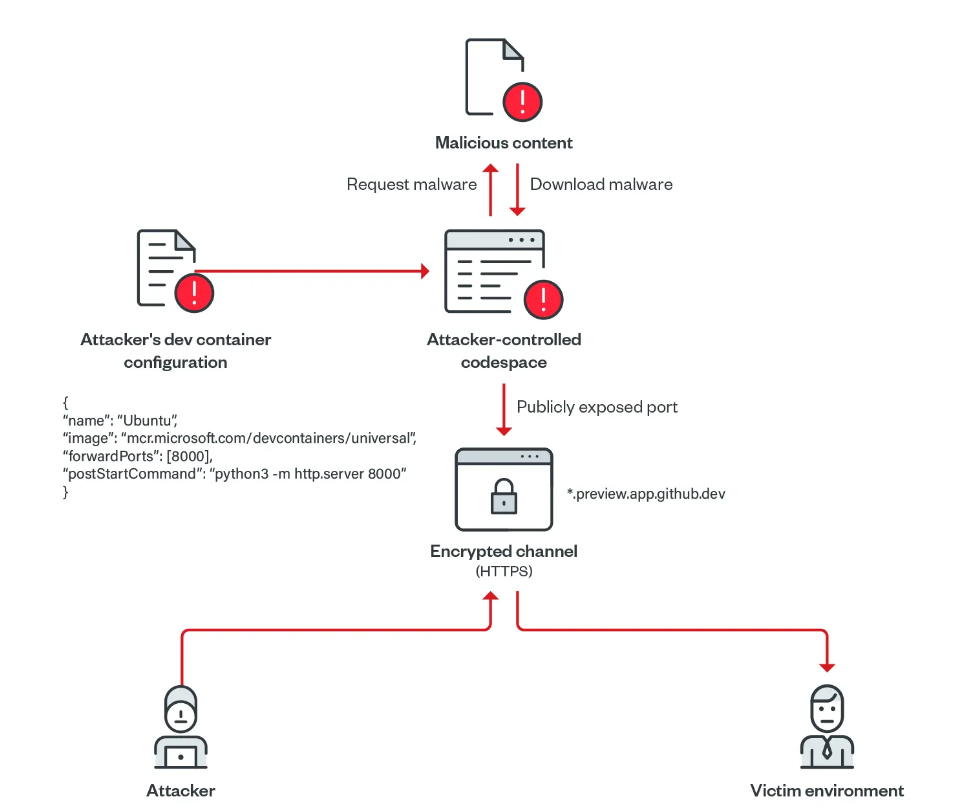
In this scenario, researchers have shown that by configuring a Codespace to act as a web server, an attacker could potentially use it to serve up malicious files or links that would be difficult for security systems to detect, because the traffic would appear to be coming from a legitimate source.
GitHub Codespaces allows developers to create and manage development environments in the cloud directly from the GitHub platform. One of the key features of Codespaces is the ability for developers to forward TCP ports to the public internet.
This means that developers can make their applications running on the Codespace available to external users by forwarding a specific port from the Codespace to the public internet.
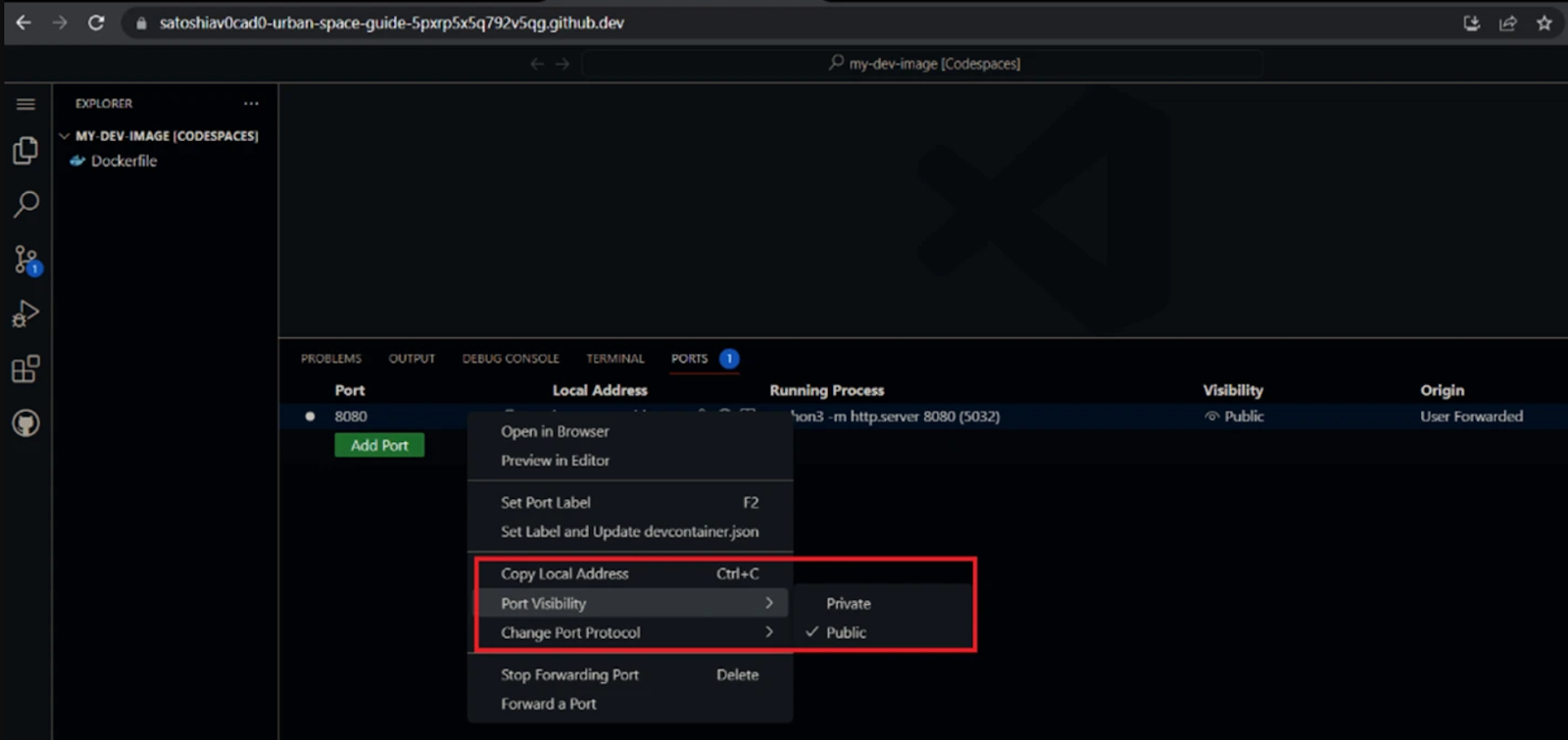
This is useful for setting up an environment for testing code, as well as for making applications accessible to others. By configuring the port as private, the URL can be shared with specific individuals, while public ports are accessible to anyone with the URL.
The main difference between a private and a public port forward is the security provided by the authentication requirement. A private port forward is much more secure since it limits access to only those who have the token or cookies, while a public port forward is open to anyone who knows the URL.
The following are possible actions an attacker could perform in theory:-
- Run a simple Python web server
- Upload malicious scripts or malware to their Codespace
- Open a web server port on their VM
- Assign it “public” visibility
Developers have the option to set the Codespaces port-forwarding system to HTTPS instead of HTTP by default. This will create the illusion that the URL is secure with respect to hackers.
The secure nature of GitHub allows threat actors to evade detection at a minimal cost since antivirus tools are less likely to raise alarms as GitHub is a trusted space.
Increasing the Attack’s Intensity
It is also possible for Trend Micro analysts to enhance their malware distribution operations by abusing the Dev Containers within GitHub Codespaces.
This tool is available to developers for quick deployment, sharing with others, and connecting to a VCS system. There are a number of things that an attacker can do by using a script, including the following:-
- Forward a port
- Run a Python HTTP server
- Download malicious files inside their Codespace
Now a web server with an open directory containing malicious files is created when the port’s visibility is set to public.
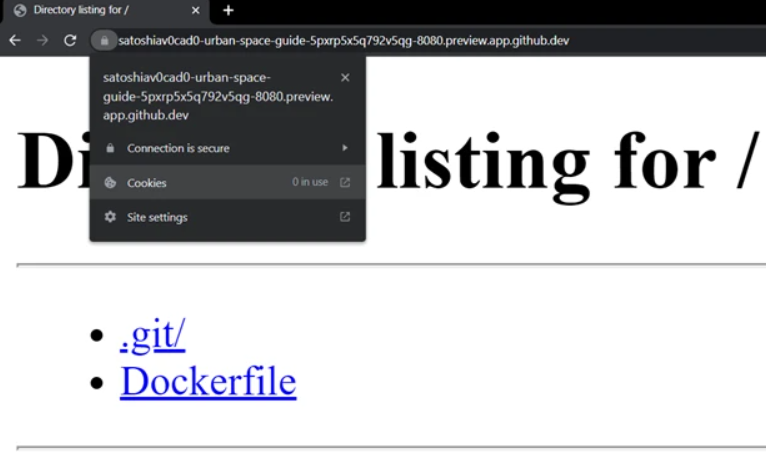
An attacker can use the same URL for an entire month because GitHub’s policy is to automatically delete inactive codespaces after 30 days. However, in response to reports of security vulnerabilities, GitHub commits to investigating them.
The company is aware of this report and plans to add a prompt to users when connecting to a codespace that asks them to confirm that they have trust in the owner.
Recommendations
Here below we have mentioned some best security practices that IT and security teams can implement to prevent future threats from abusing this platform:-
- Whenever possible, use trusted code sources, such as extensions like VSCode extensions and GitHub repositories.
- In order for developers to work with untrusted code properly, they should be aware of the repository they are working on and be careful when doing so.
- Devcontainer configuration is based upon the use of container images, which should be recognized and maintained in accordance with the requirements.
- For GitHub, you should always use passwords that are unique and strong.
- Adding two-factor authentication to your account is a great way to increase its security.
- In order to avoid credential leaks, it is necessary to avoid committing secrets and credentials publicly.
Network Security Checklist – Download Free E-Book
Source: gbhackers.com










