The prolific Iranian nation-state group known as Charming Kitten is actively targeting multiple victims in the U.S., Europe, the Middle East and India with a novel malware dubbed BellaCiao, adding to its ever-expanding list of custom tools.
Discovered by Bitdefender Labs, BellaCiao is a “personalized dropper” that’s capable of delivering other malware payloads onto a victim machine based on commands received from an actor-controlled server.
“Each sample collected was tied up to a specific victim and included hard-coded information such as company name, specially crafted subdomains, or associated public IP address,” the Romanian cybersecurity firm said in a report shared with The Hacker News.
Charming Kitten, also known as APT35, Cobalt Illusion, Educated Manticore, ITG18, Mint Sandstorm (née Phosphorus), TA453, and Yellow Garuda, is an Iranian state-sponsored APT group associated with the Islamic Revolutionary Guard Corps (IRGC).
Over the years, the group has utilized various means to deploy backdoors in systems belonging to a wide range of industry verticals.
The development comes as the threat actor was attributed by Microsoft to retaliatory attacks aimed at critical infrastructure entities in the U.S. between late 2021 to mid-2022 using bespoke malware such as harmPower, Drokbk, and Soldier.
Then earlier this week, Check Point disclosed Mint Sandstorm’s use of an updated version of the PowerLess implant to strike organizations located in Israel using Iraq-themed phishing lures.
“Custom-developed malware, also known as ‘tailored’ malware, is generally harder to detect because it is specifically crafted to evade detection and contains unique code,” Bitdefender researcher Martin Zugec noted.
The exact modus operandi used to achieve initial intrusion is currently undetermined, although it’s suspected to entail the exploitation of known vulnerabilities in internet-exposed applications like Microsoft Exchange Server or Zoho ManageEngine.
A successful breach is followed by the threat actor attempting to disable Microsoft Defender using a PowerShell command and establishing persistence on the host via a service instance.
Bitdefender said it also observed Charming Kitten downloading two Internet Information Services (IIS) modules capable of processing incoming instructions and exfiltrating credentials.
BellaCiao, for its part, is also notable for performing a DNS request every 24 hours to resolve a subdomain to an IP address that’s subsequently parsed to extract the commands to be executed on the compromised system.
“The resolved IP address is like the real public IP address, but with slight modifications that allow BellaCiao to receive further instructions,” Zugec explained.
It communicates “with an attacker-controlled DNS server that sends malicious hard-coded instructions via a resolved IP address that mimics the target’s real IP address. The result is additional malware dropped via hard-coded instructions rather than traditional download.”
Depending on the resolved IP address, the attack chain leads to the deployment of a web shell that supports the ability to upload and download arbitrary files as well as run commands.
Also spotted is a second variant of BellaCiao that substitutes the web shell for a Plink tool – a command-line utility for PuTTY – that’s designed to establish a reverse proxy connection to a remote server and implement similar backdoor features.
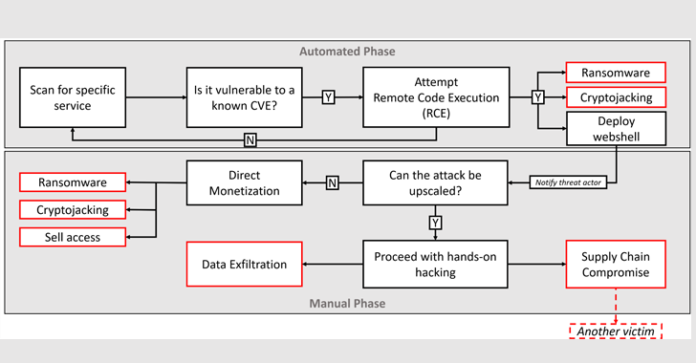
The attacks are assessed to be in the second stage after opportunistic attacks, wherein BellaCiao is customized and deployed against carefully selected victims of interest following indiscriminate exploitation of vulnerable systems.
“The best protection against modern attacks involves implementing a defense-in-depth architecture,” Zugec concluded. “The first step in this process is to reduce the attack surface, which involves limiting the number of entry points that attackers can use to gain access to your systems and prompt patching of newly discovered vulnerabilities.”
Source: thehackernews.com