The cybersecurity researchers at ESET recently made a significant discovery, a previously unidentified remote access trojan (RAT) lurking within an Android screen recording app, available for download on the Google Play Store and already amassed tens of thousands of installations.
The ‘iRecorder – Screen Recorder’ app, initially introduced in September 2021, was potentially compromised through a malicious update in August 2022, utilizing its name to deceive users by requesting audio recording and file access permissions under the guise of a legitimate screen recording application.
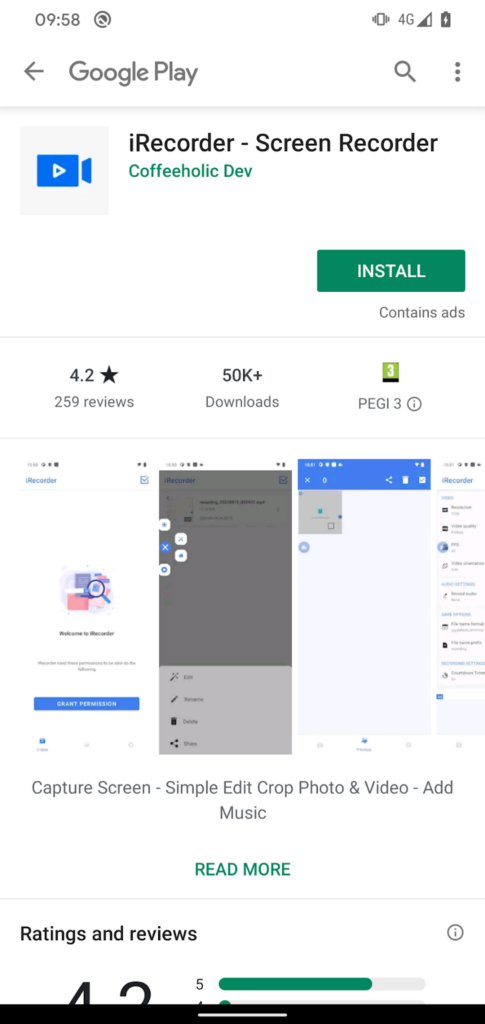
While apart from this, the app has achieved more than 50,000 installations on the Google Play Store before its removal, raising the concern for users of exposure to malware infection.
After being notified, iRecorder was removed from the Google Play store due to its malicious behavior, but it can still be obtained from unofficial Android markets.
In addition to offering other applications on Google Play, the developer of iRecorder ensures that their apps are free from any malicious code or harmful elements.
Android Malware on Google Play
The malware known as AhRat, derived from the open-source Android RAT AhMyth, has extensive capabilities encompassing device tracking and more.
Here below, we have mentioned all the capabilities it offers to its operators:-
- Location
- Stealing call logs
- Contacts
- Text messages
- Sending SMS messages
- Taking pictures
- Recording background audio
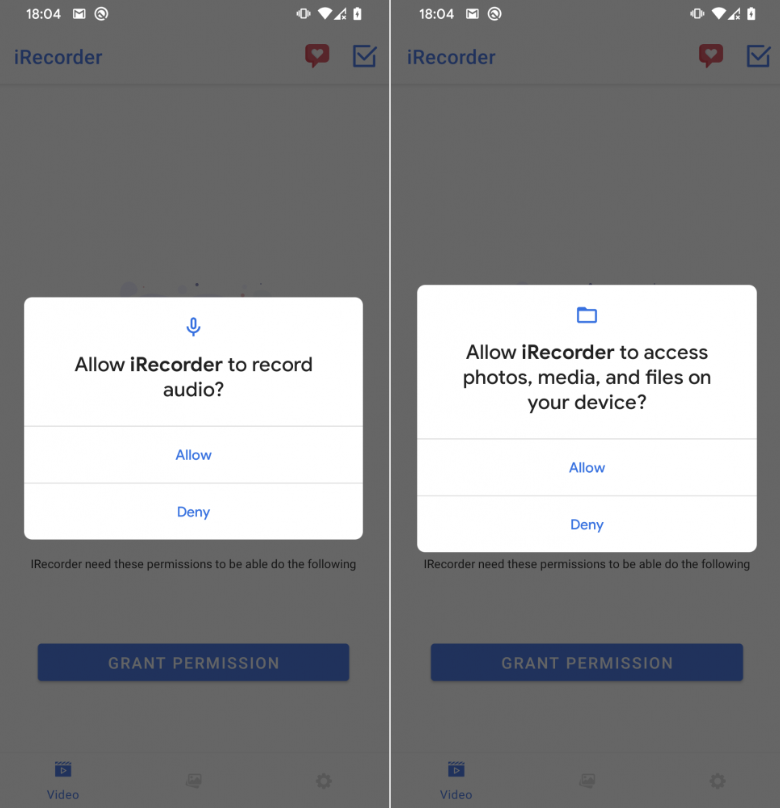
ESET discovered that the malicious screen recording app utilized only a portion of the RAT’s functions, focusing on capturing ambient sound and stealing files of certain extensions, suggesting potential involvement in espionage.
Moreover, ESET previously exposed a case in 2019 where AhMyth-based Android malware successfully evaded Google Play’s security checks twice by disguising itself as a radio streaming app, highlighting a recurring issue with AhMyth infiltration on the platform.
AhRat initiates communication with the C&C server upon installation by sharing essential device details while simultaneously receiving encryption keys and a configuration file in encrypted form.

Following the initial communication, AhRat establishes a regular connection with the C&C server, sending periodic pings every 15 minutes to request an updated configuration file.
AhRat is designed to execute 18 commands based on the instructions received in the configuration file from the C&C server. But, the RAT can execute the six commands only exclusively that we have mentioned below:-
- RECORD_MIC
- FILE_LIST
- UPLOAD_FILE_AFTER_DATE
- LIMIT_UPLOAD_FILE_SIZE
- UPLOAD_FILE_TYPE
- UPLOAD_FILE_FOLDER
However, Android 11 and subsequent versions have already incorporated proactive measures such as App hibernation to safeguard against such malicious activities.
The hibernation feature resets runtime permissions of dormant apps, preventing their intended malicious activities, and the subsequent removal of the malicious app from Google Play reinforces the importance of multi-layered protection.
Shut Down Phishing Attacks with Device Posture Security – Download Free E-Book
Source: gbhackers.com