ESET researchers have recently discovered that Linux users targeted with malware in the new “Operation DreamJob” Lazarus campaign for the first time.
The group behind DreamJob deploys social engineering tactics with the guise of fake job offers as lures to compromise its targets.
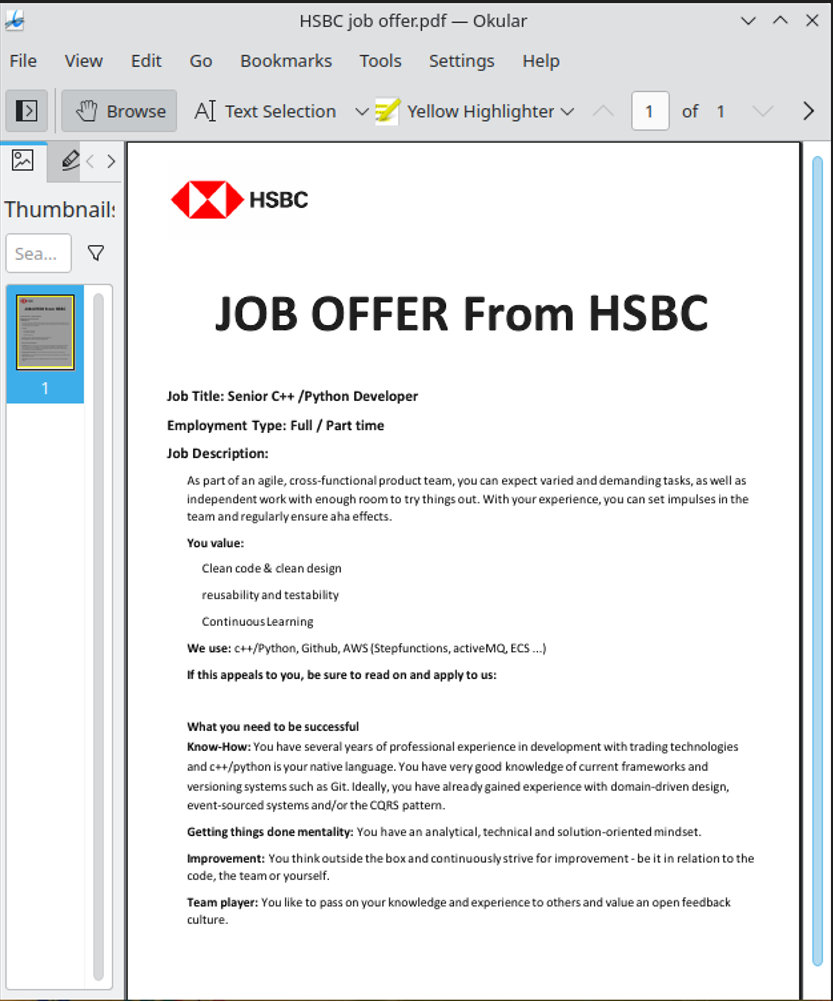
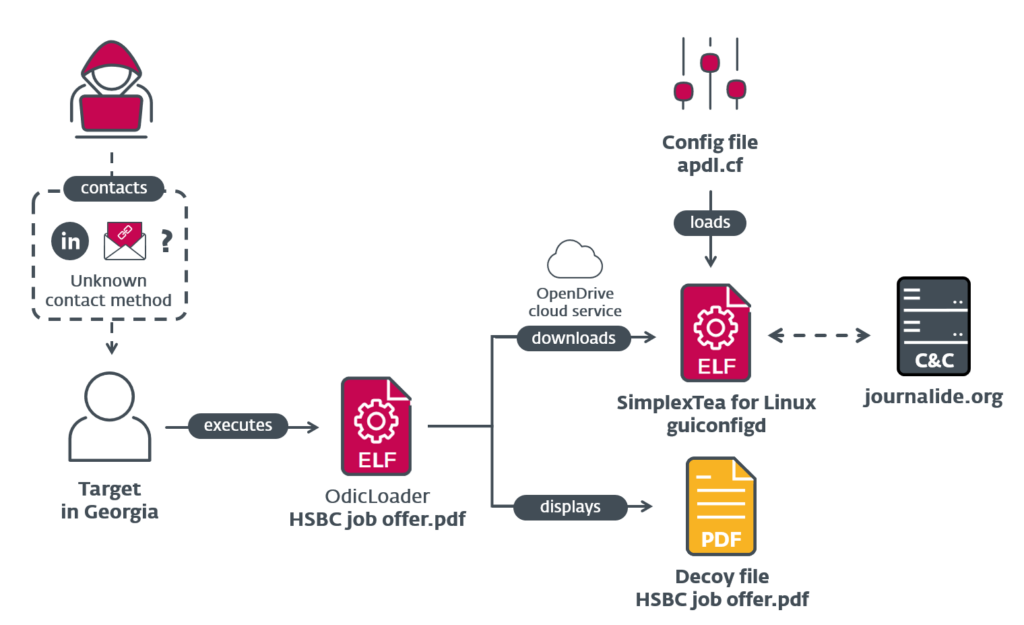
Experts could reconstruct the complete sequence by tracing the chain from a false HSBC job offer in a ZIP file to the distribution of the SimplexTea Linux backdoor via an OpenDrive cloud storage account.
This North Korea-linked threat actor’s use of Linux malware in this operation is publicly mentioned for the first time. This discovery also enabled experts to confirm that Lazarus was responsible for the 3CX supply-chain attack.
3CX Supply-chain Attack
Many companies rely on 3CX for their phone systems service, as it is one of the leading international providers of VoIP and telephone services.
There are more than 600,000 customers available to 3CX, and in the following sectors, it also has more than 12,000,000 users:-
- Aerospace
- Healthcare
- Hospitality
The discovery of malicious code in the desktop application for Windows and macOS was made in March 2023.
While this allowed the downloading and running of arbitrary code on all machines with the installed application by a group of attackers.
As a result, the 3CX software was hacked, and external attackers used it to distribute malware to specific customers as part of a supply-chain attack.
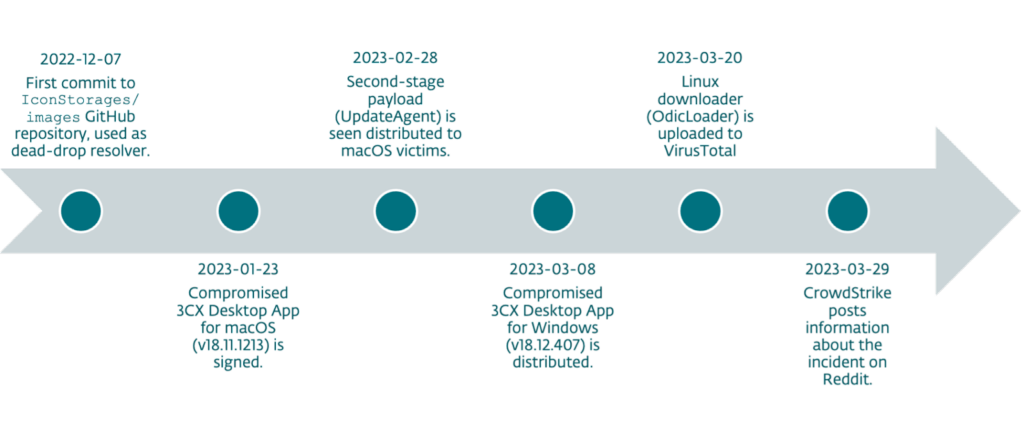
Here Below we have mentioned the timeline:-
Operation Dream Job
The group behind Operation Dream Job (aka DeathNote or NukeSped) uses fake job offers to trick people into downloading malware in multiple attack waves.
At the moment, it’s unclear how the ZIP file was distributed, but spear-phishing or direct messages on LinkedIn are the suspected methods.
These social engineering attacks deceive victims into downloading files that infect their computers with malware by posing as employment-related documents, ESET Says.
Apart from this, the backdoor written in C++ has the same appearance as the one previously associated with the group called BADCALL, it’s another Windows trojan.
The ZIP archive that is in question is distributed via spearphishing or direct messages on LinkedIn and the archive is named:-
A Linux binary written in Go is hidden inside the archive, which is named with a Unicode character to appear as a PDF file.
The filename’s extension isn’t “.pdf” because the apparent dot is a U+2024 Unicode character that serves as a leader dot.
The leader dot in the filename was likely a trick to fool the file manager into running the file as an executable rather than a PDF, leading to unintended execution upon double-clicking.
Double-clicking the file launches the OdicLoader malware, which downloads a second-stage malware from a private repository on OpenDrive while displaying a fake PDF document as a decoy.
OdicLoader delivers the SimplexTea payload, which it drops at ~/.config/guiconfigd/SimplexTea, and alters the user’s ~/.bash_profile to ensure that SimplexTea runs with Bash and remains silenced during new shell sessions.
Supply-chain attacks are a favored method of malware distribution for their stealthiness, and Lazarus used this technique in 2020 to target South Korean users of WIZVERA VeraPort software.
Previous Operation DreamJob attacks by Lazarus were incredibly lucrative, resulting in the group’s theft of $620 million from Axie Infinity.
The techniques and similarities observed in the recent 3CX hack align with the Lazarus group’s typical modus operandi and toolset, indicating their strong involvement.
Moreover, the notorious group Lazarus has claimed another high-profile win with their recent supply-chain attack on 3CX.
Building Your Malware Defense Strategy – Download Free E-Book
Source: gbhackers.com











