An exhaustive analysis of FIN7 has unmasked the cybercrime syndicate’s organizational hierarchy, alongside unraveling its role as an affiliate for mounting ransomware attacks.
It has also exposed deeper associations between the group and the larger threat ecosystem comprising the now-defunct ransomware DarkSide, REvil, and LockBit families.
The highly active threat group, also known as Carbanak, is known for employing an extensive arsenal of tools and tactics to expand its “cybercrime horizons,” including adding ransomware to its playbook and setting up fake security companies to lure researchers into conducting ransomware attacks under the guise of penetration testing.
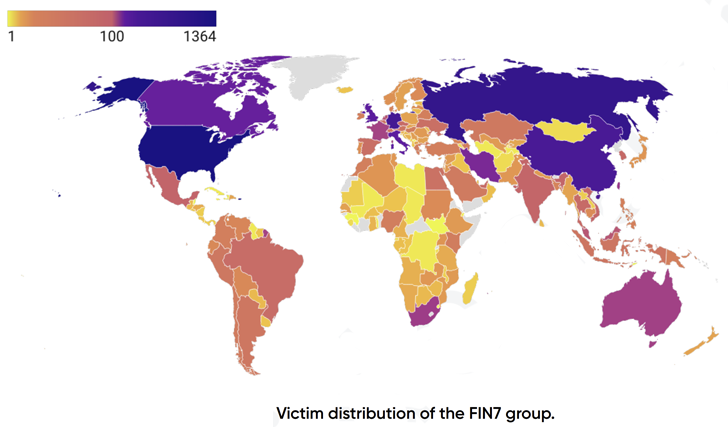
More than 8,147 victims have been compromised by the financially motivated adversary across the world, with a majority of the entities located in the U.S. Other prominent countries include China, Germany, Canada, Italy, and the U.K.
FIN7’s intrusion techniques, over the years, have further diversified beyond traditional social engineering to include infected USB drives, software supply chain compromise and the use of stolen credentials purchased from underground markets.
“Nowadays, its initial approach is to carefully pick high-value companies from the pool of already compromised enterprise systems and force them to pay large ransoms to restore their data or seek unique ways to monetize the data and remote access,” PRODAFT said in a report shared with The Hacker News.
According to the Swiss cybersecurity company, the threat actors have also been observed to weaponize flaws in Microsoft Exchange such as CVE-2020-0688, CVE-2021-42321, ProxyLogon, and ProxyShell flaws in Microsoft Exchange Server to obtain a foothold into target environments.

The use of double extortion tactics notwithstanding, attacks mounted by the group have deployed backdoors on the compromised systems, even in scenarios where the victim has already paid a ransom.
The idea is to resell access to other ransomware outfits and re-target the victims as part of its illicit money-making scheme, underscoring its attempts to minimize efforts and maximize profits, not to mention prioritize companies based on their annual revenues, founded dates, and the number of employees.
This “demonstrates a particular type of feasibility study considered a unique behavior among cybercrime groups,” the researchers said.
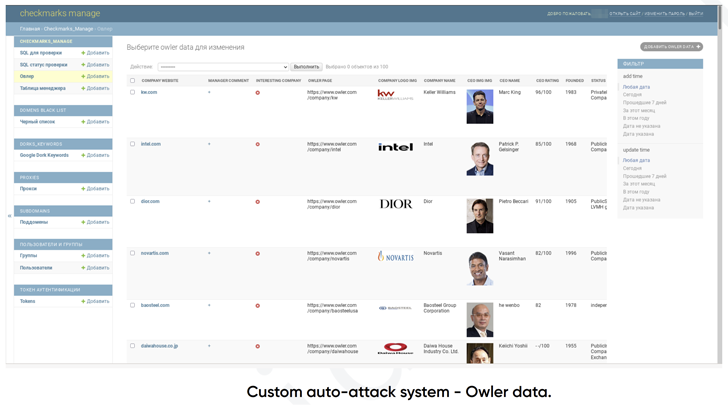
Put differently, the modus operandi of FIN7 boils down to this: It utilizes services like Dun & Bradstreet (DNB), Crunchbase, Owler, and Zoominfo to shortlist firms and organizations with the highest revenue. It also uses other website analytics platforms like MuStat and Similarweb to monitor traffic to the victims’ sites.
Initial access is then obtained through one of the many intrusion vectors, followed by exfiltrating data, encrypting files, and eventually determining the ransom amount based on the company’s revenue.
These infection sequences are also designed to load the remote access trojans such as Carbanak, Lizar (aka Tirion), and IceBot, the latter of which was first documented by Recorded Future-owned Gemini Advisory in January 2022.
Other tools developed by FIN7 encompass modules to automate scans for vulnerable Microsoft Exchange servers and other public-facing web applications as well as Cobalt Strike for post-exploitation.
In yet another indication that criminal groups function like traditional companies, FIN7 follows a team structure consisting of top-level management, developers, pentesters, affiliates, and marketing teams, each of whom are tasked with individual responsibilities.
While two members named Alex and Rash are the chief players behind the operation, a third managerial member named Sergey-Oleg is responsible for delegating duties to the group’s other associates and overseeing their execution.
However, it has also been observed that operators in administrator positions engage in coercion and blackmail to intimidate team members into working more and issue ultimatums to “hurt their family members in case of resigning or escaping from responsibilities.”
The findings come more than a month after cybersecurity company SentinelOne identified potential links between FIN7 and the Black Basta ransomware operation.
“FIN7 has established itself as an extraordinarily versatile and well-known APT group that targets enterprise companies,” PRODAFT concluded.
“Their signature move is to thoroughly research the companies based on their revenue, employee count, headquarters and website information to pinpoint the most profitable targets. Although they have internal issues related to the unequal distribution of obtained monetary resources and somewhat questionable practices towards their members, they have managed to establish a strong presence in the cybercrime sphere.”
Source: thehackernews.com










