The cybersecurity researchers at Sucuri recently discovered a critical backdoor that has managed to infiltrate thousands of websites over the past few months.
A group of threat actors who are responsible for a malware campaign called “black hat redirect” has increased the scope of their operation by incorporating more than 70 fake domains that imitate URL shortening services.
The attackers have managed to infect a significant number of websites with this malware, with the current count surpassing 10,890.
Visitors are Being Directed to Hacked Sites
The primary goal of the operation remains ad fraud, which involves the use of illicit techniques to artificially boost the volume of traffic to web pages featuring AdSense IDs and Google ads. This activity is carried out with the intent of generating revenue through fraudulent means.
Recently, various Google products such as Google Ads, Google Home, and Google Drive have been used to disseminate malware and other harmful components. This has been confirmed as a factual occurrence and has raised concerns about the security and safety of these products.
GoDaddy’s subsidiary company first revealed the malicious activity in November 2022, after the company was acquired by the GoDaddy corporation.
This campaign began in September last year and is redirecting visitors to compromised WordPress sites to fake question-and-answer portals. This is a potential threat to the security and privacy of individuals who may unknowingly disclose sensitive information.
Apparently, this aims to increase the authority of spammy sites in search engines so that they will appear higher in search results.
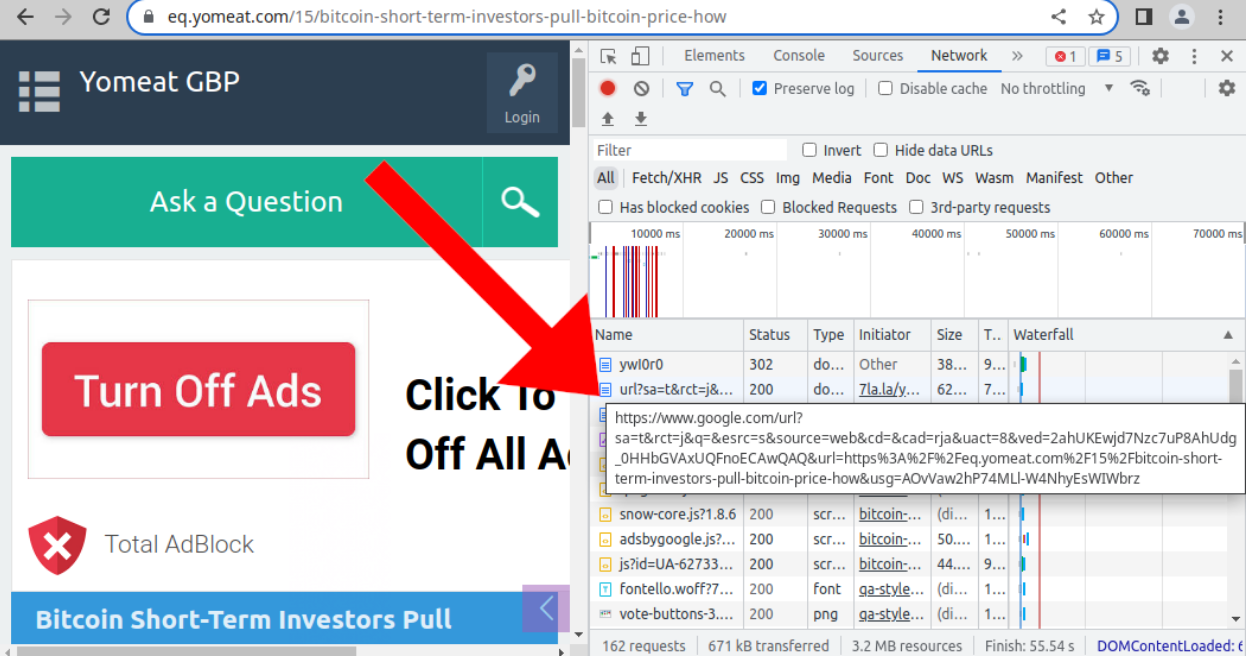
Similar to the previous malware attack, it has been observed that the latest wave of malware is also attempting to redirect internet traffic through Google searches. By doing so, the attackers aim to make the redirected traffic occur legit.
Abusing URL Shorteners
Sucuri detected that all of the infected websites were using the WordPress content management system. As a result of this, legitimate files on the websites had been corrupted with an obfuscated PHP script.
The latest campaign has a significant feature that sets it apart from previous ones. In their redirects, it makes use of Bing search result links, Twitter’s link shortener service, and Google as well.
The campaign’s utilization of these services suggests a strategic move to evade detection by security measures. This indicates an expansion of the threat actor’s footprint.
Attack Analysis
Sucuri researchers have recently discovered more than 75 pseudo-short URL domains that are associated with redirected traffic. This discovery has been made over the course of the last two months.
It is important to highlight that the majority of malicious URLs discovered are linked to a single URL-shortening service. All the low-quality Question2Answer websites are completely related to cryptocurrency or blockchain technology.
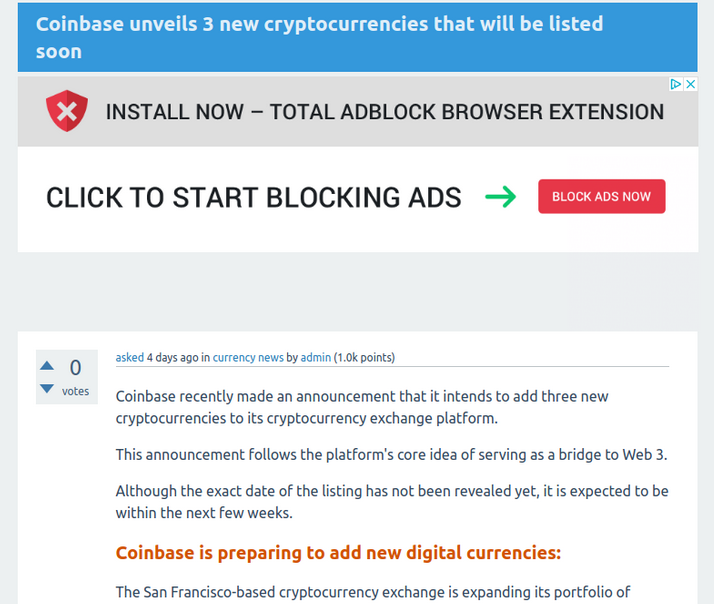
It has been suggested that these advertisements may be part of an intentional pump-and-dump ICO fraud where new cryptocurrencies are advertised.
Despite the lack of conclusive evidence, researchers are confident that the main aim of ad fraud is to artificially boost website traffic in order to display Google ads and generate revenue through AdSense ID.
These malicious websites have been known to inject obfuscated code into critical files, such as wp-blog-header.php. This code can cause harm by manipulating the behavior of the affected website and potentially compromising the security of its users.
In order to ensure that the malware is not detected and disinfected, this code acts as a backdoor. In an effort to conceal itself, the malware adopts the strategy of pausing redirections for a period of 2 to 6 hours whenever an administrator logs in or a user visits an infected site.
This makes it difficult for website administrators to detect the presence of the malware, as its activity is temporarily suspended during these instances. In order to hide the malicious code, Base64 encoding is used.
AdSense IDs Used
Here below we have mentioned all the AdSense IDs that are used on the websites that are infected:-
- en[.]rawafedpor[.]com: ca-pub-8594790428066018
- plus[.]cr-halal[.]com: ca-pub-3135644639015474
- eq[.]yomeat[.]com: ca-pub-4083281510971702
- news[.]istisharaat[.]com: ca-pub-6439952037681188
- en[.]firstgooal[.]com: ca-pub-5119020707824427
- ust[.]aly2um[.]com: ca-pub-8128055623790566
- btc[.]latest-articles[.]com: ca-pub-4205231472305856
- ask[.]elbwaba[.]com: ca-pub-1124263613222640, ca-pub-1440562457773158
Mitigation
Here below we have mentioned all the mitigations recommended by the experts to the website owners:-
- Ensure that all software is updated to the most recent version and make sure it is patched.
- Ensure that the admin area of your WordPress website has 2FA security or other access restrictions.
- Immediately change all the panel and database passwords.
- Make sure to use strong and unique passwords with several variations.
- Protect your website against attacks by placing it behind a firewall.
Network Security Checklist – Download Free E-Book
Source: gbhackers.com











